

 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
 This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
This essay argues that Internet governance has drifted from technical coordination into unaccountable institutional power, and proposes "Running-Code Primacy" as a post-RIR framework grounded in distributed validation, interoperability, and voluntary adoption rather than registry authority.
 Three decades after Iridium's costly collapse, falling launch costs and improved signal processing are reviving satellite-to-phone ambitions, as Starlink, Amazon and AST SpaceMobile race to build direct-to-device networks that could reshape mobile coverage and competition.
Three decades after Iridium's costly collapse, falling launch costs and improved signal processing are reviving satellite-to-phone ambitions, as Starlink, Amazon and AST SpaceMobile race to build direct-to-device networks that could reshape mobile coverage and competition.
 Jan Žorž reflects on SEE RIPE's role in uniting a fragmented region, where trust built through informal exchange now underpins internet resilience and helps align engineers with policymakers as regulatory pressures intensify.
Jan Žorž reflects on SEE RIPE's role in uniting a fragmented region, where trust built through informal exchange now underpins internet resilience and helps align engineers with policymakers as regulatory pressures intensify.
 Subsea cables underpin global data flows, yet resilience, control and deep sea access now define digital sovereignty as governance fragments, hyperscalers consolidate ownership, and states prioritize survivability over efficiency in an increasingly contested geopolitical seabed.
Subsea cables underpin global data flows, yet resilience, control and deep sea access now define digital sovereignty as governance fragments, hyperscalers consolidate ownership, and states prioritize survivability over efficiency in an increasingly contested geopolitical seabed.
 As AI agents scale, IP reputation emerges as a hidden constraint, shaping access to external systems and degrading performance. Managing network identity, not just models, is becoming essential for reliable data collection.
As AI agents scale, IP reputation emerges as a hidden constraint, shaping access to external systems and degrading performance. Managing network identity, not just models, is becoming essential for reliable data collection.
 Community networks, locally built and governed, are emerging across Africa as cost-effective tools to extend connectivity, bolster digital sovereignty, and improve cyber resilience, despite regulatory, financial, and technical constraints that hinder broader adoption.
Community networks, locally built and governed, are emerging across Africa as cost-effective tools to extend connectivity, bolster digital sovereignty, and improve cyber resilience, despite regulatory, financial, and technical constraints that hinder broader adoption.
 Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
 AI agents are rapidly becoming primary internet users, with inference-driven traffic reshaping network demands and exposing infrastructure blind spots as latency-sensitive, machine-to-machine activity begins to outpace and outcompete human web behavior.
AI agents are rapidly becoming primary internet users, with inference-driven traffic reshaping network demands and exposing infrastructure blind spots as latency-sensitive, machine-to-machine activity begins to outpace and outcompete human web behavior.
 Surging outages and mounting losses are increasingly forcing a rethink of network operations, as NOGs now confront a shift from technical exchange to strategic governance, where resilience, leadership, and institutional influence define the profession's future.
Surging outages and mounting losses are increasingly forcing a rethink of network operations, as NOGs now confront a shift from technical exchange to strategic governance, where resilience, leadership, and institutional influence define the profession's future.
 CaribNOG's 32nd forum in Curaçao marks a shift from volunteer roots to institutional structure, as the Caribbean network community formalises programmes, expands research, and positions itself to tackle climate, geopolitical, and infrastructure pressures.
CaribNOG's 32nd forum in Curaçao marks a shift from volunteer roots to institutional structure, as the Caribbean network community formalises programmes, expands research, and positions itself to tackle climate, geopolitical, and infrastructure pressures.
 As governments, firms and engineers reshape networks, the internet is fragmenting into rival systems. Interoperability erodes, raising costs, curbing rights and weakening resilience, with global growth, innovation and cooperation increasingly at risk.
As governments, firms and engineers reshape networks, the internet is fragmenting into rival systems. Interoperability erodes, raising costs, curbing rights and weakening resilience, with global growth, innovation and cooperation increasingly at risk.
 A dispute over African IP governance exposes a flaw in the RIR system, where thin policy, weak accountability and institutional self preservation risk overriding running networks and undermining the technical legitimacy that sustained global coordination.
A dispute over African IP governance exposes a flaw in the RIR system, where thin policy, weak accountability and institutional self preservation risk overriding running networks and undermining the technical legitimacy that sustained global coordination.
 Critics blame IPv4 markets for inequality, but registry rules long rewarded scale and imposed regressive costs. Scarcity was managed, not equalized, leaving poorer networks paying more for slower, less predictable access over time and regions.
Critics blame IPv4 markets for inequality, but registry rules long rewarded scale and imposed regressive costs. Scarcity was managed, not equalized, leaving poorer networks paying more for slower, less predictable access over time and regions.
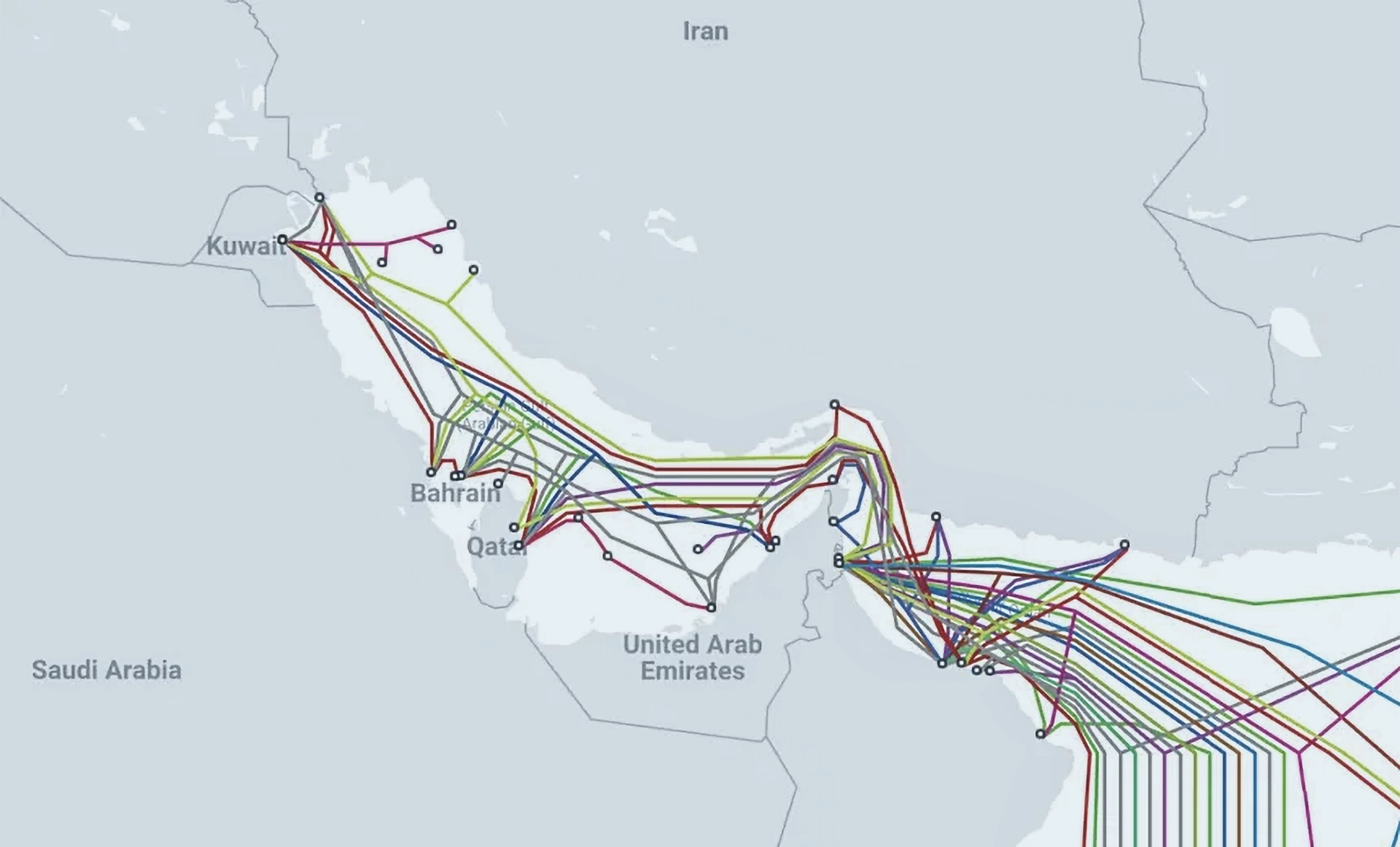 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears US Senators Move to Shield Undersea Internet Cables from Global Threats
US Senators Move to Shield Undersea Internet Cables from Global Threats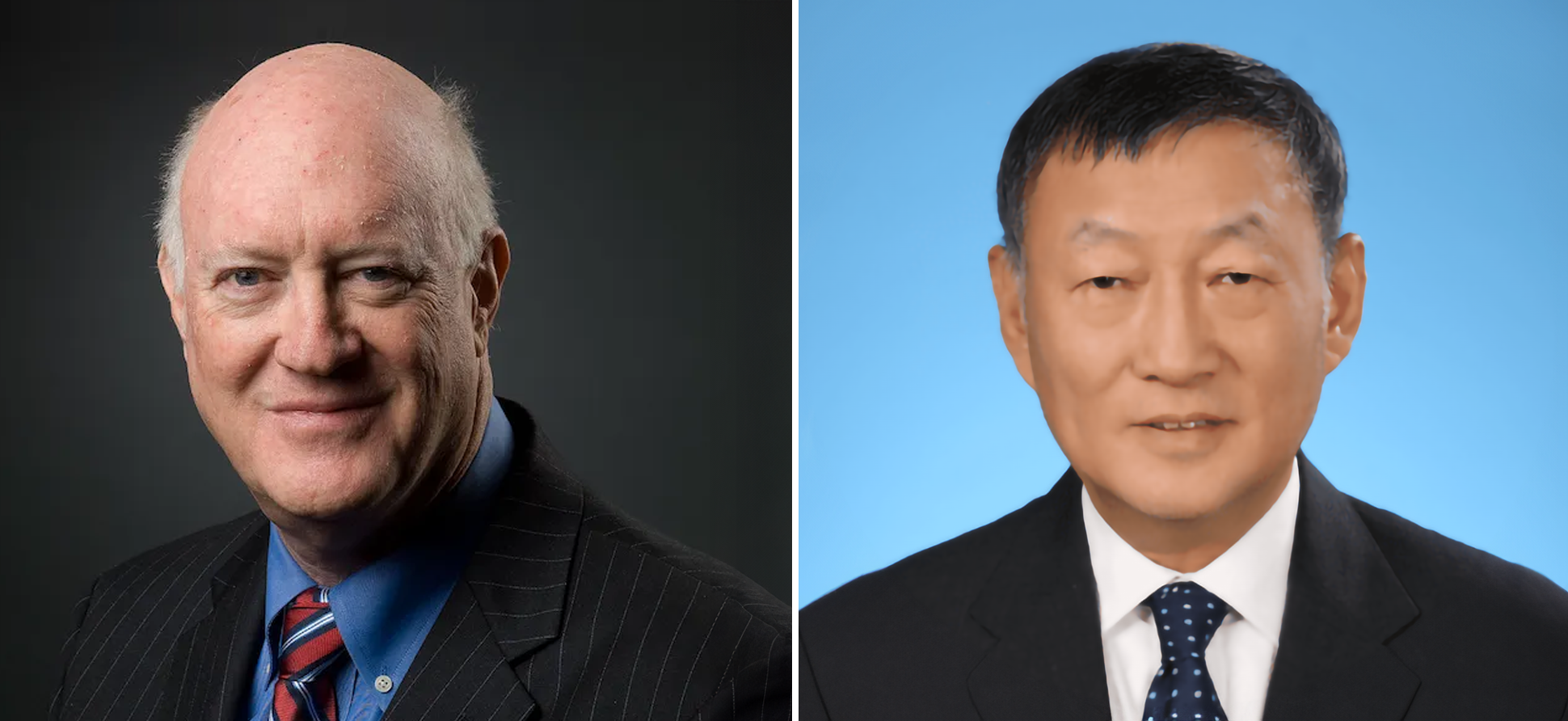 Internet Visionaries Honored with Postel Service Award
Internet Visionaries Honored with Postel Service Award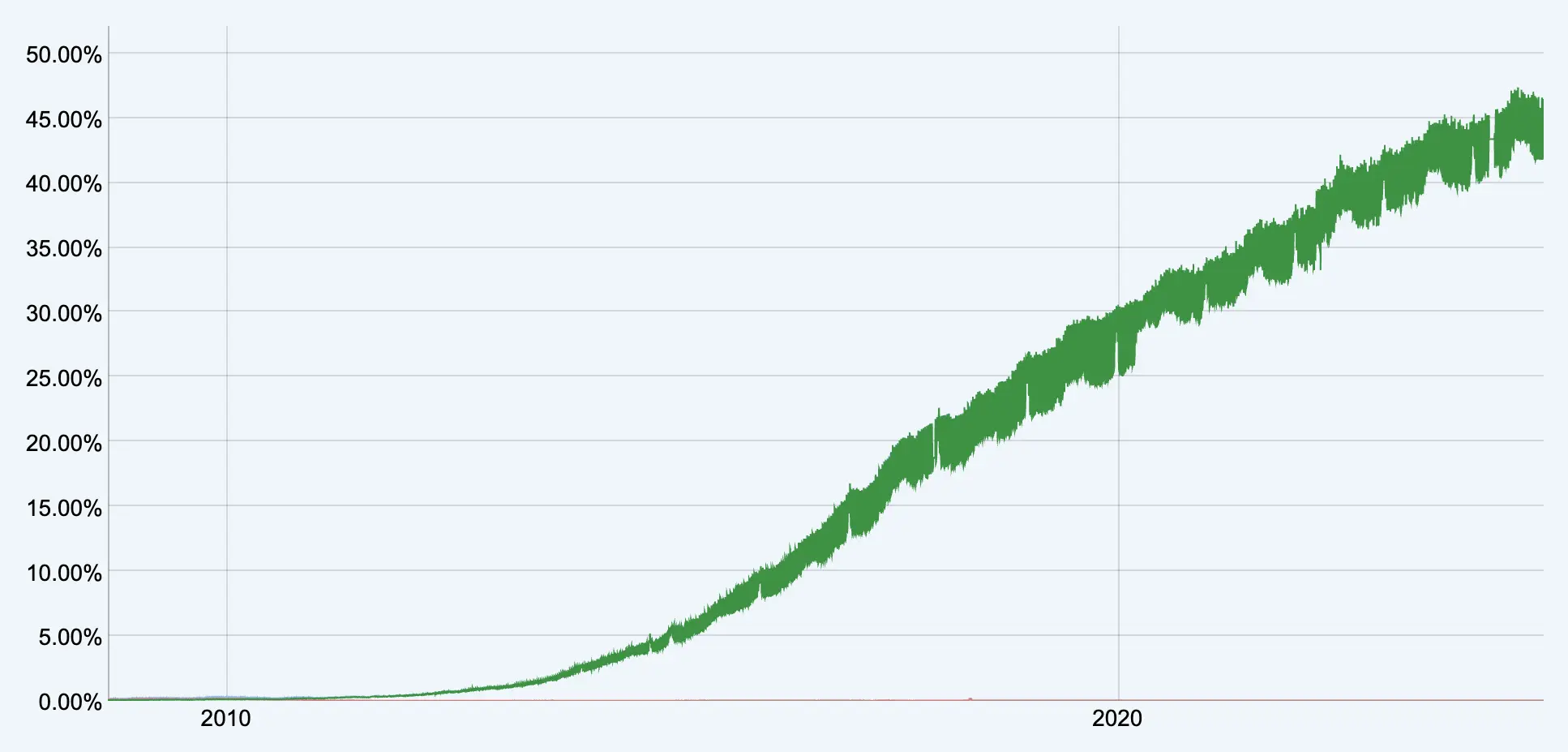 IPv6 Transition Stalls as Internet Moves Beyond IP Addresses
IPv6 Transition Stalls as Internet Moves Beyond IP Addresses Global IT Outage Disrupts Airlines, Businesses, and Hospitals
Global IT Outage Disrupts Airlines, Businesses, and Hospitals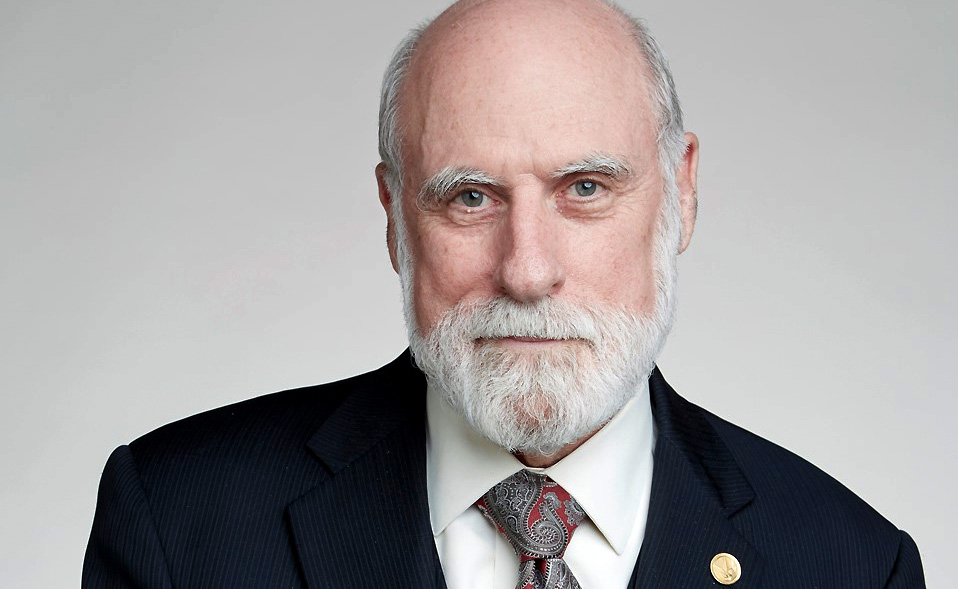 Vint Cerf Receives IEEE Medal of Honor
Vint Cerf Receives IEEE Medal of Honor