

 Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
Fake recruitment websites exploiting India's young job seekers are proliferating, exposing millions to identity theft, financial fraud and malware while regulators, registrars and digital literacy programs struggle to keep pace with a growing labor market.
 Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
 Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
 Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
 Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
 A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
 Africa's rapid digital expansion, from fintech to e-government, is outpacing its cybersecurity capacity, leaving critical systems exposed and trust at risk unless governments embed security as a core pillar of development across the continent today.
Africa's rapid digital expansion, from fintech to e-government, is outpacing its cybersecurity capacity, leaving critical systems exposed and trust at risk unless governments embed security as a core pillar of development across the continent today.
 GlobalBlock's expansion into China and Germany signals a shift from reactive brand protection to centralized prevention, as firms seek scalable, cost efficient defences against proliferating AI driven domain abuse worldwide amid a fragmented digital landscape.
GlobalBlock's expansion into China and Germany signals a shift from reactive brand protection to centralized prevention, as firms seek scalable, cost efficient defences against proliferating AI driven domain abuse worldwide amid a fragmented digital landscape.
 ICANN's new DNS abuse rules mark progress, yet short-term domain leasing enables fleeting, hard-to-detect attacks. A proposed 30-day minimum lease could curb cybercrime by undermining the economics of weaponised parked domains.
ICANN's new DNS abuse rules mark progress, yet short-term domain leasing enables fleeting, hard-to-detect attacks. A proposed 30-day minimum lease could curb cybercrime by undermining the economics of weaponised parked domains.
 America's FCC has barred new foreign-made consumer routers on security grounds, tightening supply for ISPs and households while raising costs and risking technological lag unless domestic manufacturing or approvals quickly expand in coming years significantly.
America's FCC has barred new foreign-made consumer routers on security grounds, tightening supply for ISPs and households while raising costs and risking technological lag unless domestic manufacturing or approvals quickly expand in coming years significantly.
 The UN's new permanent cybersecurity mechanism promises continuity after decades of fleeting forums, yet risks irrelevance unless states enforce existing law, bridge cybercrime divides, address AI threats, build practical capacity, and include non-state expertise meaningfully.
The UN's new permanent cybersecurity mechanism promises continuity after decades of fleeting forums, yet risks irrelevance unless states enforce existing law, bridge cybercrime divides, address AI threats, build practical capacity, and include non-state expertise meaningfully.
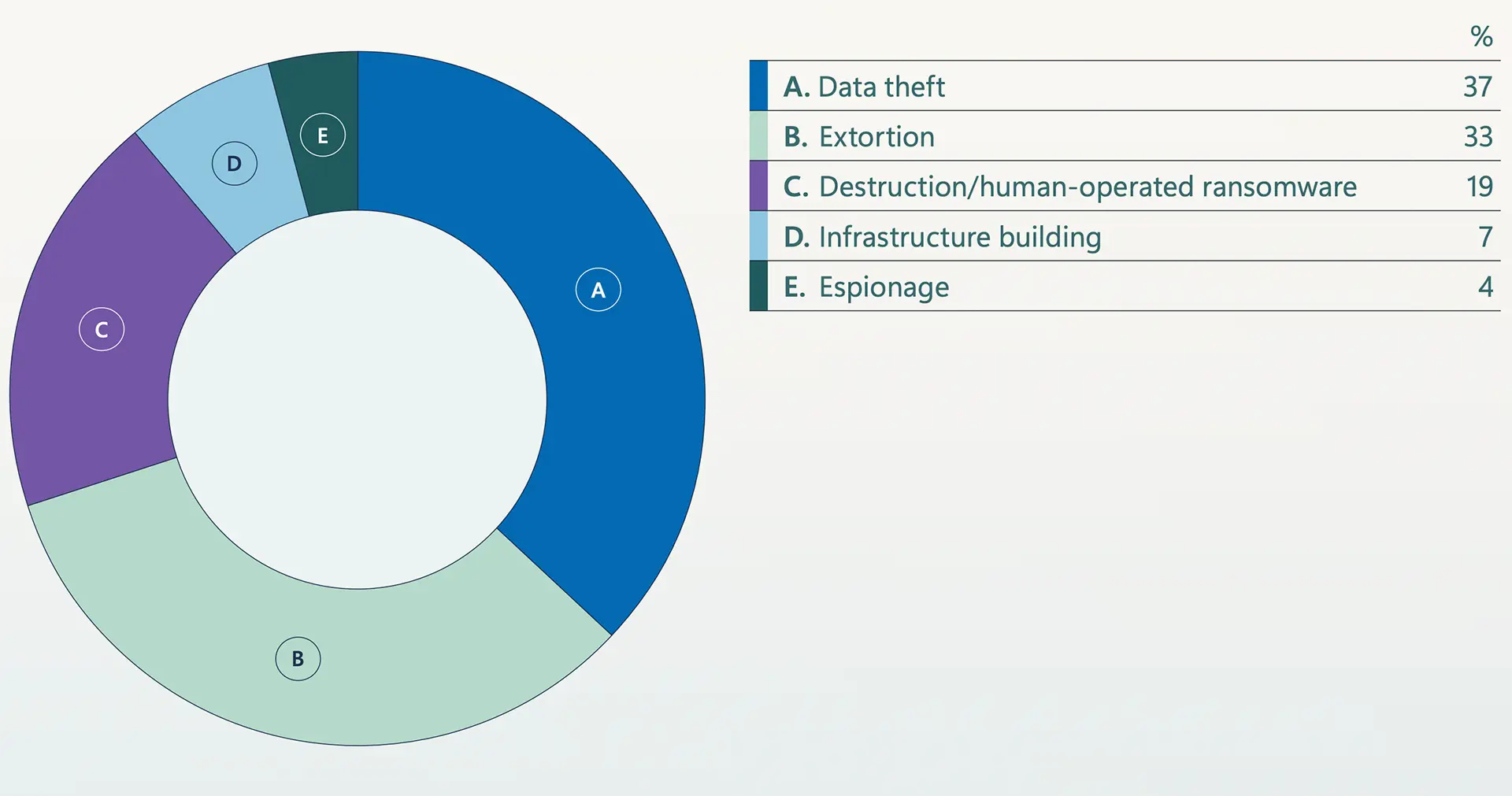 Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation
Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation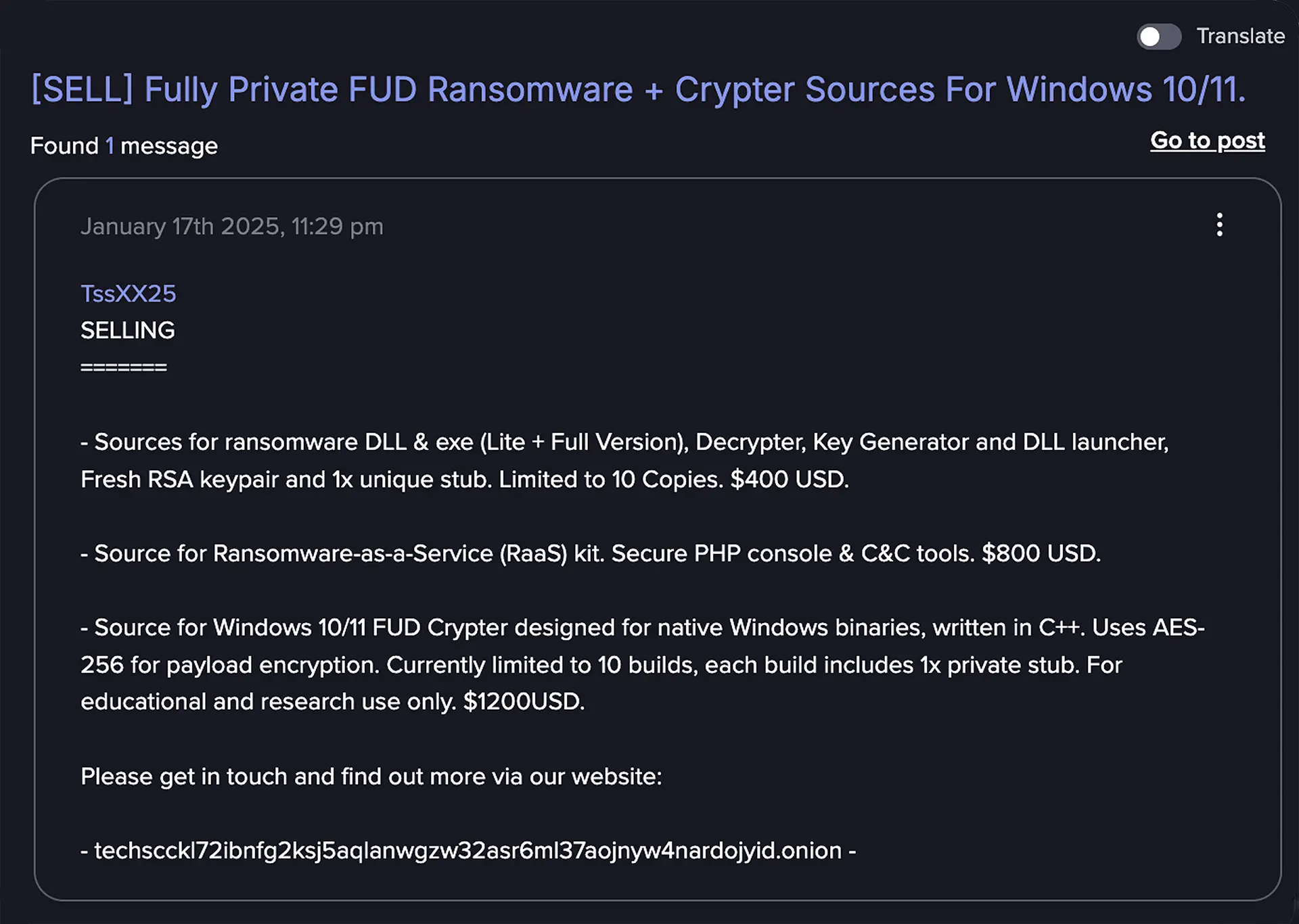 Advanced AI Is Reshaping the Cybercriminal Landscape at Alarming Speed
Advanced AI Is Reshaping the Cybercriminal Landscape at Alarming Speed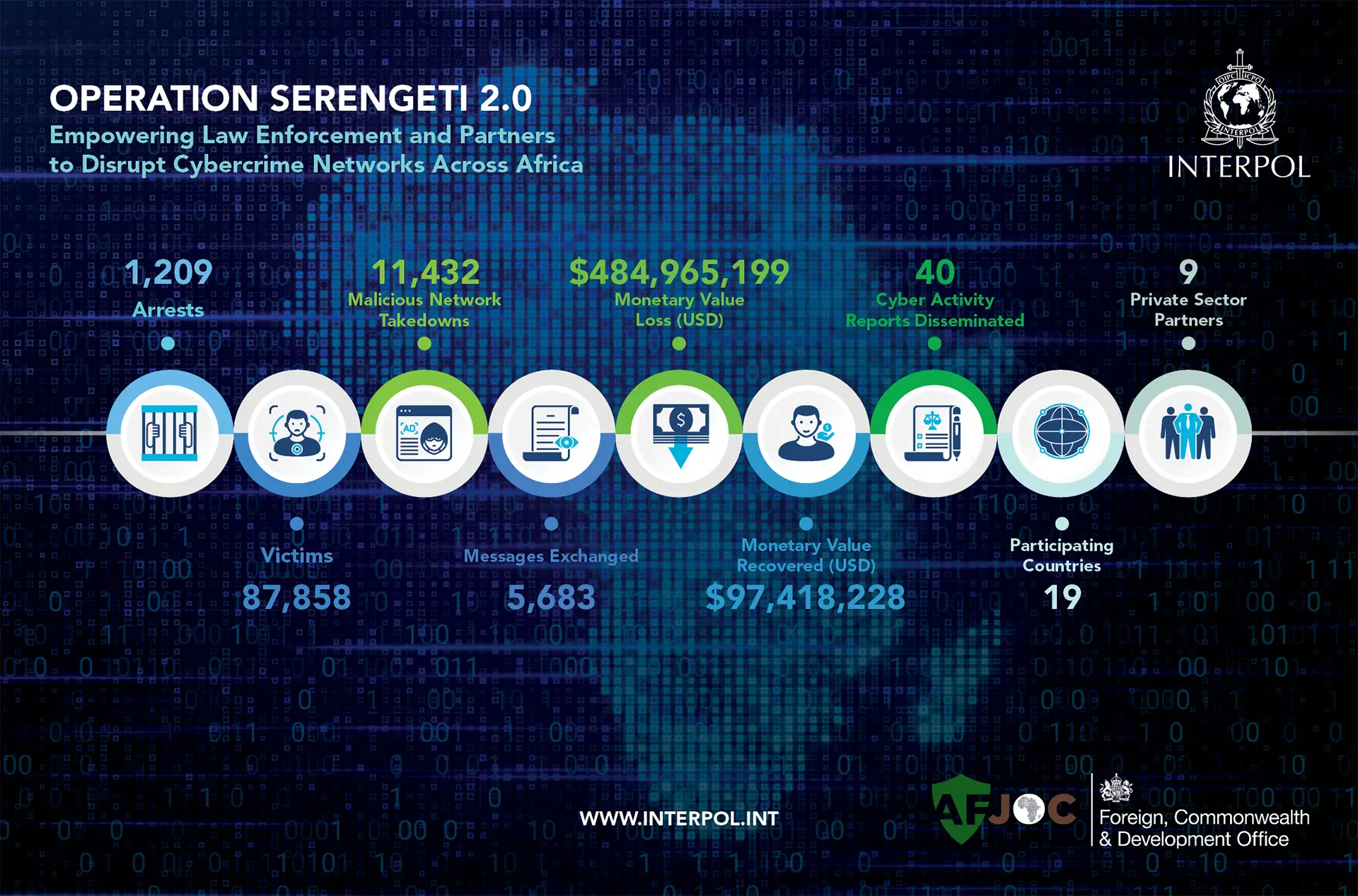 INTERPOL Leads Arrest of 1,209 Suspects in Pan-African Cybercrime Crackdown, Recovers $97 Million
INTERPOL Leads Arrest of 1,209 Suspects in Pan-African Cybercrime Crackdown, Recovers $97 Million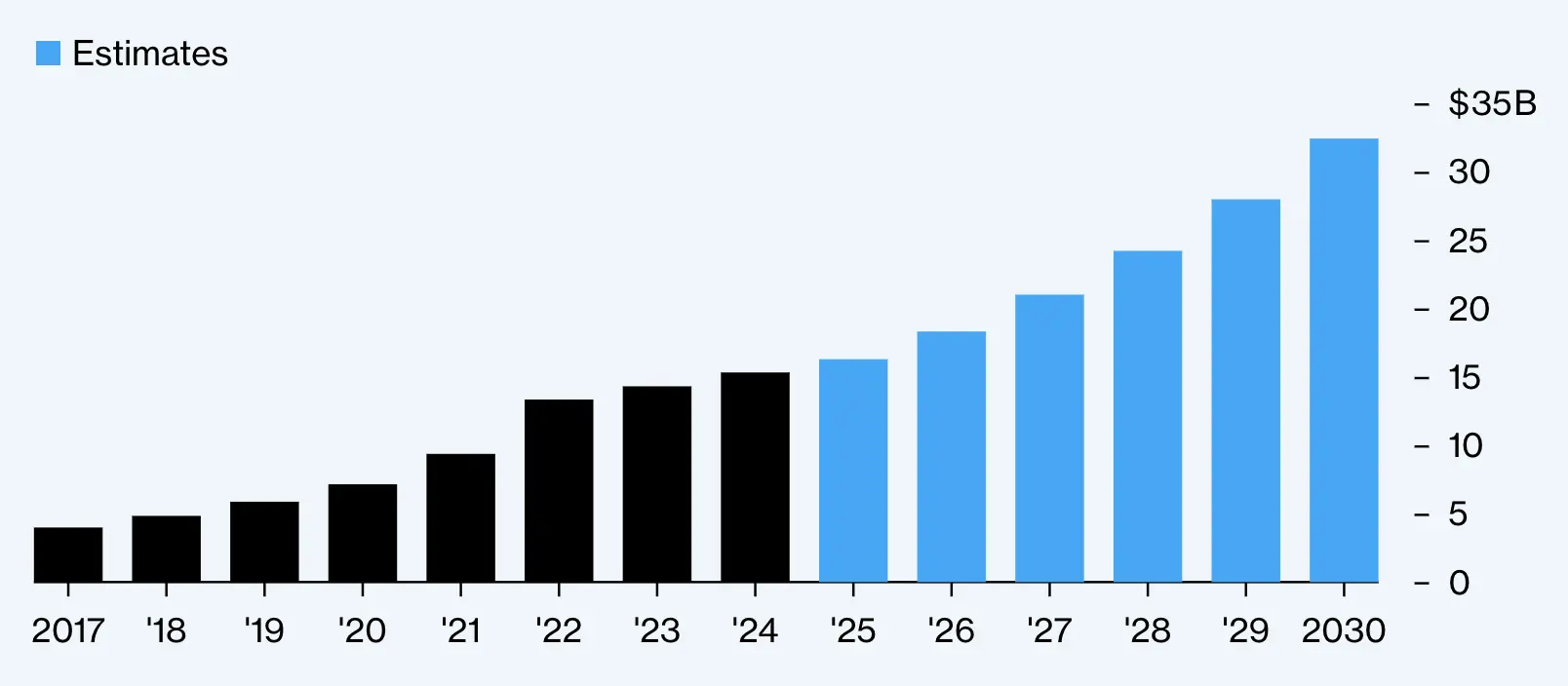 Cyberattacks Spur Boom in Insurance Demand Amid Rising Global Threats
Cyberattacks Spur Boom in Insurance Demand Amid Rising Global Threats India Launches ‘.bank.in’ and ‘.fin.in’ Domains to Deter Financial Fraud
India Launches ‘.bank.in’ and ‘.fin.in’ Domains to Deter Financial Fraud Biden Administration to Back UN Cybercrime Treaty Amid Controversy
Biden Administration to Back UN Cybercrime Treaty Amid Controversy Ransomware Crisis in U.S. Healthcare
Ransomware Crisis in U.S. Healthcare Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation
Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation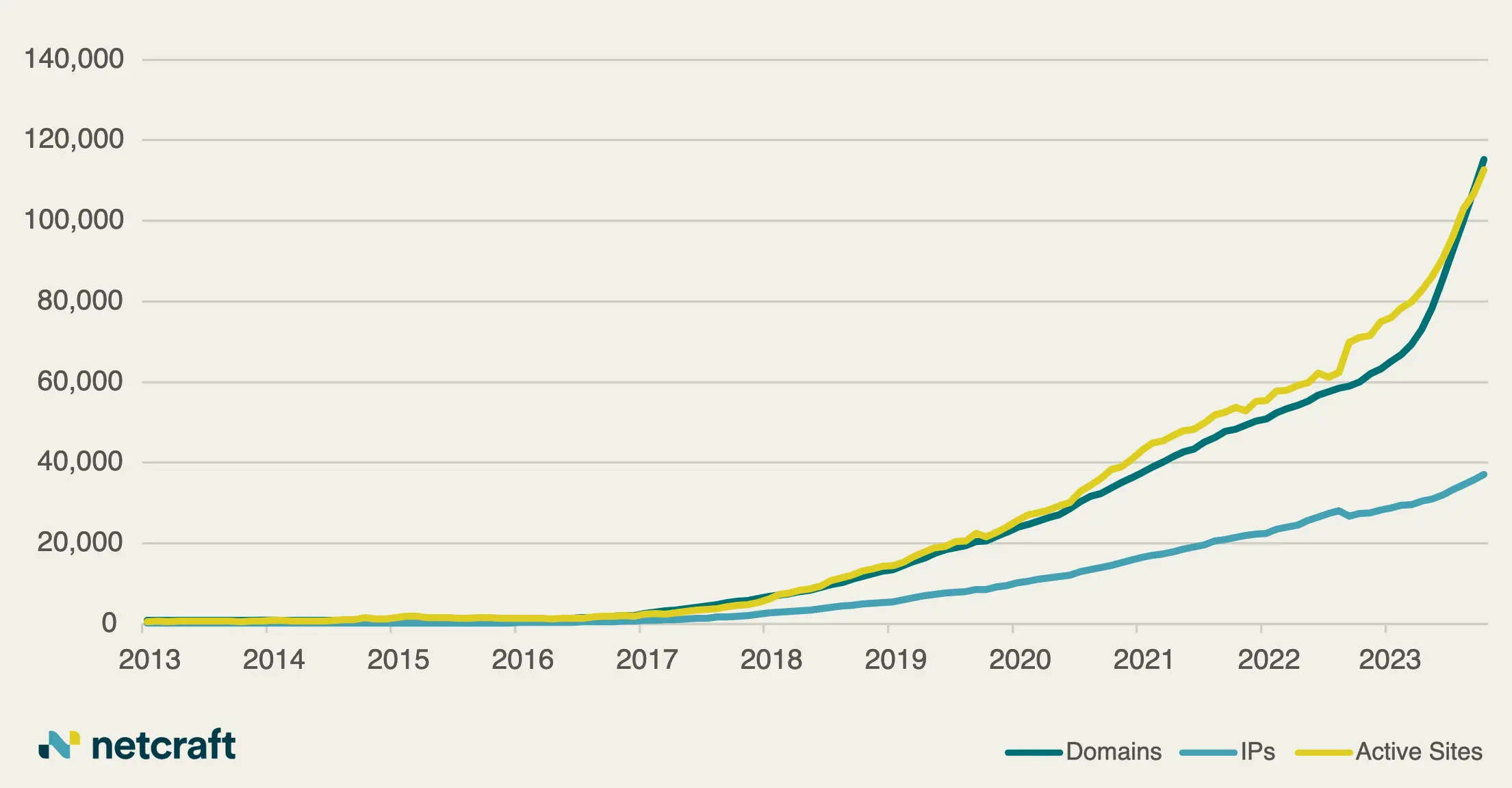 Rise in Cybercrime Exploiting Artificial Intelligence Hype Leads to Growing Threats Within the .ai Domain Space
Rise in Cybercrime Exploiting Artificial Intelligence Hype Leads to Growing Threats Within the .ai Domain Space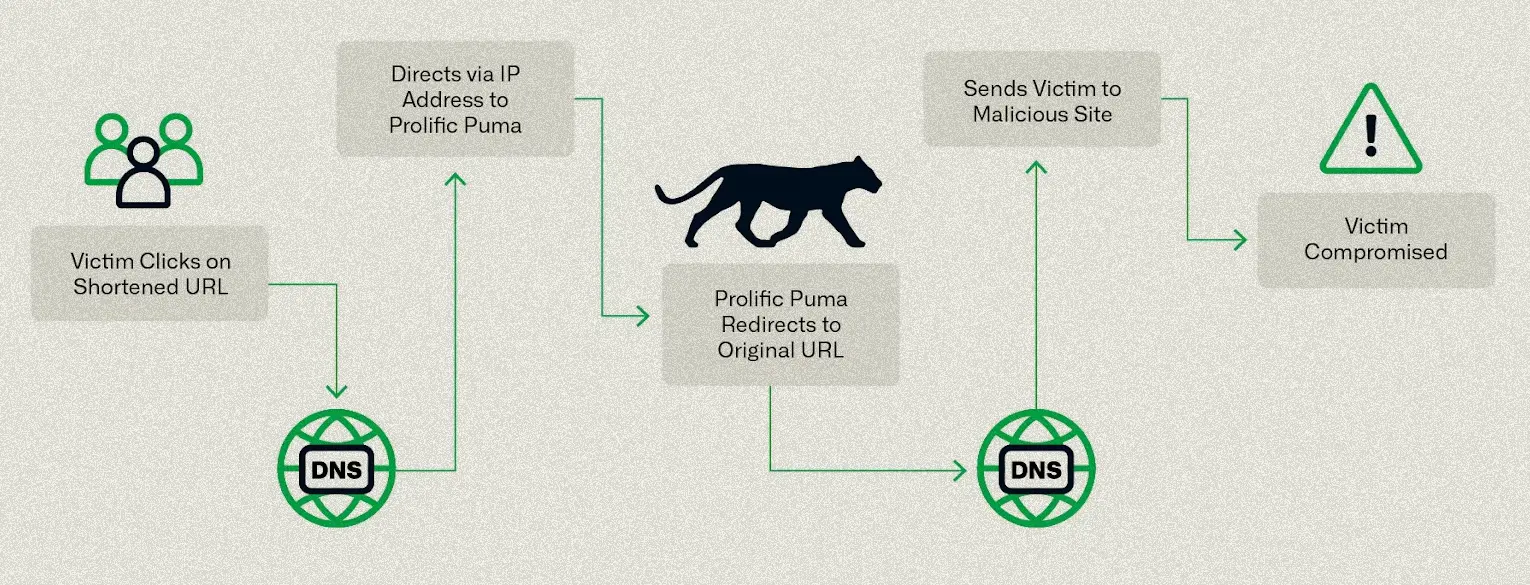 Researchers Uncover Massive Underground Link-Shortening Service Used by Malicious Actors
Researchers Uncover Massive Underground Link-Shortening Service Used by Malicious Actors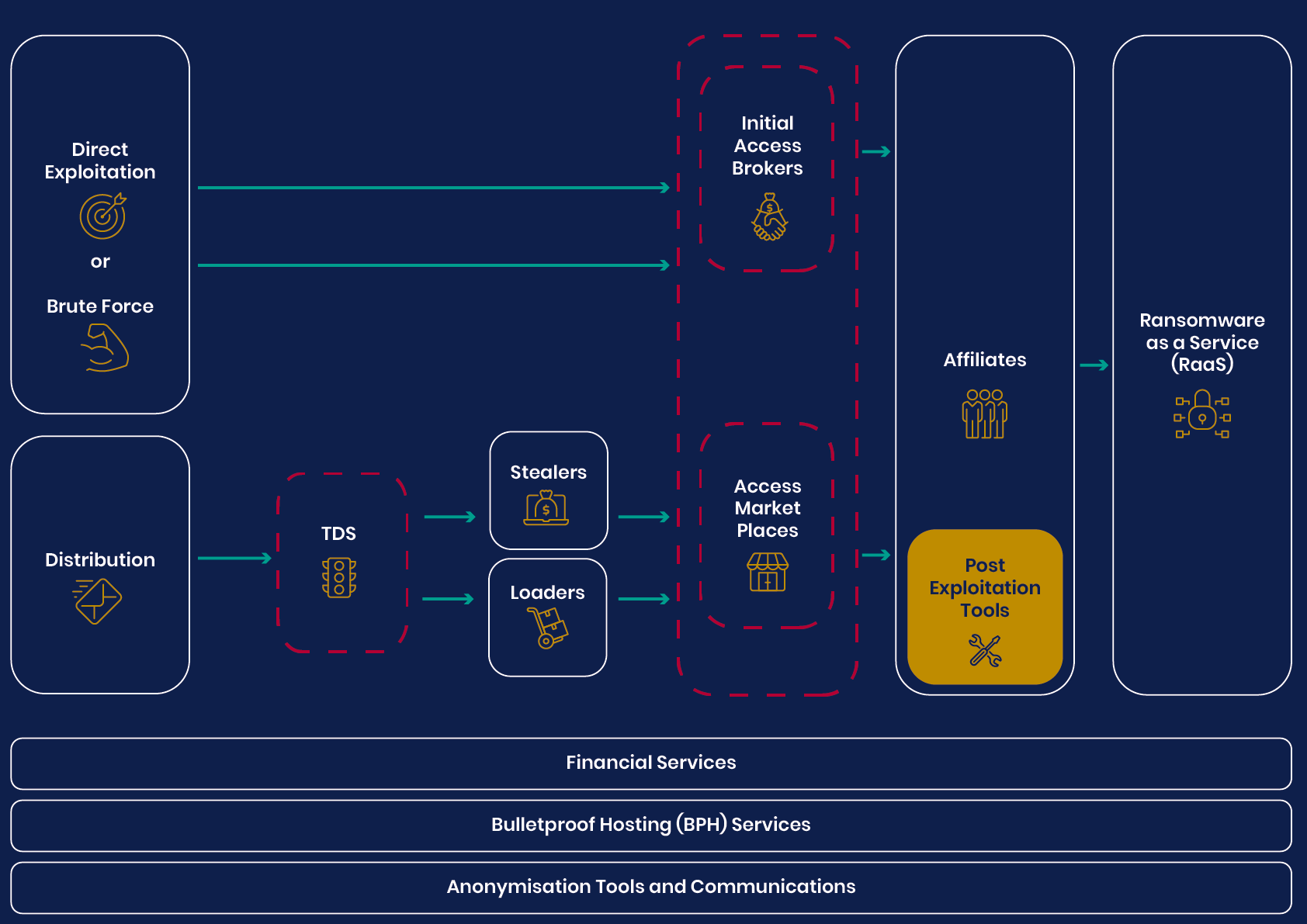 UK’s National Agencies Release White Paper on Evolving Cyber Crime Ecosystem
UK’s National Agencies Release White Paper on Evolving Cyber Crime Ecosystem The Hague to Probe Cyberwarfare Under Existing International Law
The Hague to Probe Cyberwarfare Under Existing International Law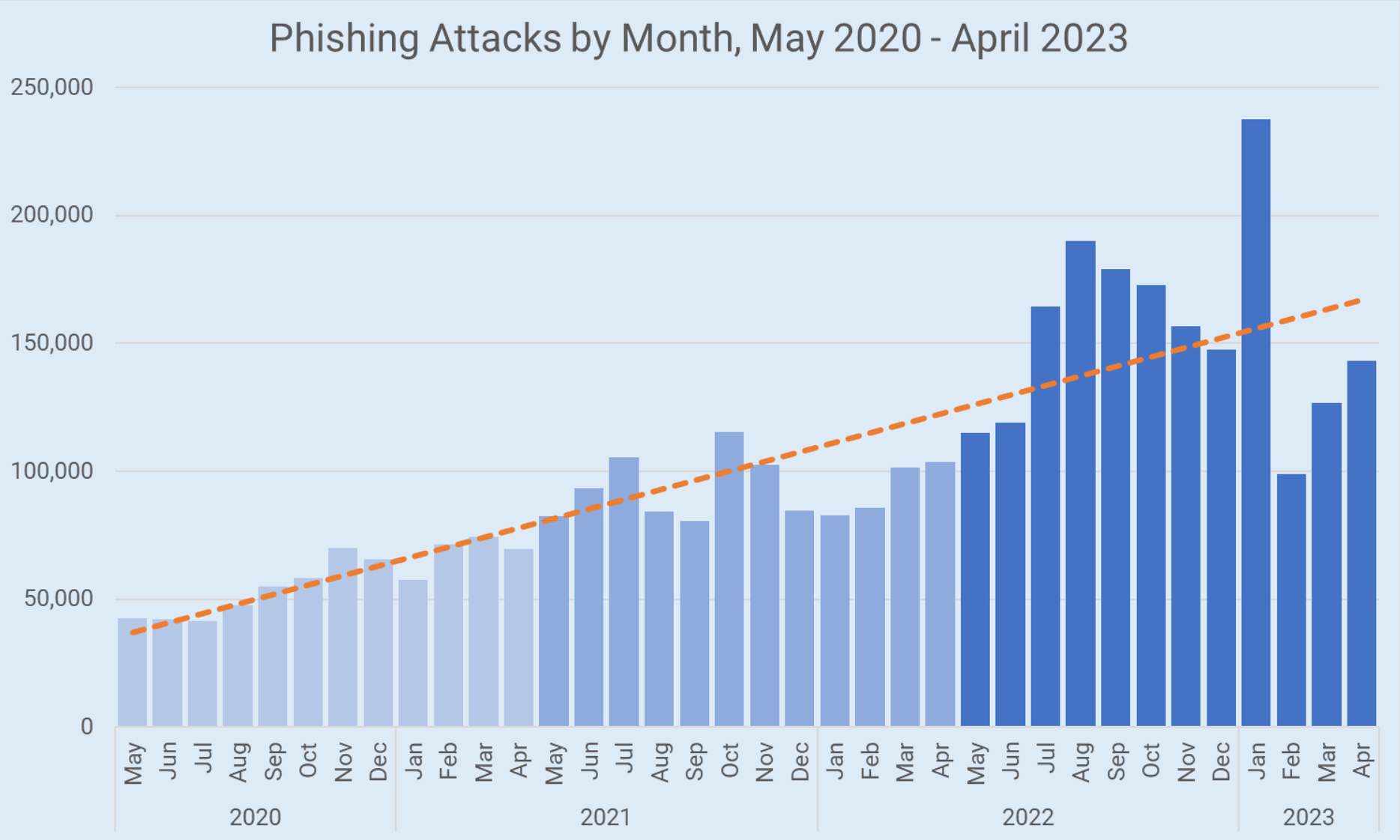 Phishing Attacks Surge Despite Increased Awareness, New Strategies Needed
Phishing Attacks Surge Despite Increased Awareness, New Strategies Needed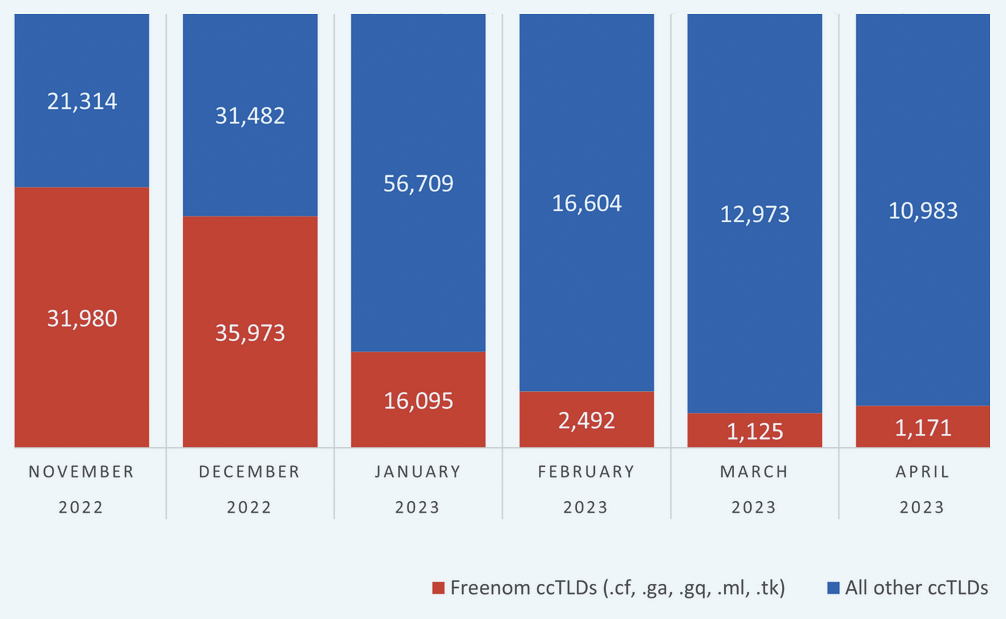 Meta Lawsuit Leads to Significant Decline in Phishing Domains Tied to Freenom
Meta Lawsuit Leads to Significant Decline in Phishing Domains Tied to Freenom