

 Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
Missile strikes on Gulf data centres exposed a deeper contradiction at the heart of digital sovereignty: governments seek territorial control over internet infrastructure whose resilience still depends upon globally distributed coordination and interdependence across borders.
 Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
Africa's digital boom is accelerating, but safeguards lag. Governments and firms deploy systems at speed, while weak enforcement and fragmented oversight leave economies exposed to mounting cyber risks.
 Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
Third-party domains exploiting brand names are proliferating, with 88% of homoglyphs externally owned. Many remain dormant yet email-enabled, creating scalable phishing risks as attackers increasingly target trust rather than infrastructure.
 Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
 Kinetic attacks on Gulf data centres expose the cloud's physical fragility, recasting AI infrastructure as strategic targets and accelerating bunkerisation, while outdated data laws leave firms choosing between legal compliance and digital survival.
Kinetic attacks on Gulf data centres expose the cloud's physical fragility, recasting AI infrastructure as strategic targets and accelerating bunkerisation, while outdated data laws leave firms choosing between legal compliance and digital survival.
 Africa's rapid digital expansion, from fintech to e-government, is outpacing its cybersecurity capacity, leaving critical systems exposed and trust at risk unless governments embed security as a core pillar of development across the continent today.
Africa's rapid digital expansion, from fintech to e-government, is outpacing its cybersecurity capacity, leaving critical systems exposed and trust at risk unless governments embed security as a core pillar of development across the continent today.
 America's FCC has barred new foreign-made consumer routers on security grounds, tightening supply for ISPs and households while raising costs and risking technological lag unless domestic manufacturing or approvals quickly expand in coming years significantly.
America's FCC has barred new foreign-made consumer routers on security grounds, tightening supply for ISPs and households while raising costs and risking technological lag unless domestic manufacturing or approvals quickly expand in coming years significantly.
 The FCC warns telecom companies of rising ransomware threats after attacks quadrupled since 2022. The agency urges stronger defenses including patching, multifactor authentication, network segmentation, and closer oversight of vendors and incident response planning.
The FCC warns telecom companies of rising ransomware threats after attacks quadrupled since 2022. The agency urges stronger defenses including patching, multifactor authentication, network segmentation, and closer oversight of vendors and incident response planning.
 Iran's near-total internet blackout during airstrikes reveals how cyberattacks, sanctions and platform power can isolate a nation. The conflict shows digital infrastructure, satellites and cloud services becoming decisive weapons in modern geopolitical competition worldwide today.
Iran's near-total internet blackout during airstrikes reveals how cyberattacks, sanctions and platform power can isolate a nation. The conflict shows digital infrastructure, satellites and cloud services becoming decisive weapons in modern geopolitical competition worldwide today.
 Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
 At Munich's twin security gatherings, leaders warned that cyber conflict, transatlantic rifts and weaponised AI are pushing the rules-based order into a perilous transition, where deterrence falters, norms erode and digital sovereignty trumps multistakeholder ideals.
At Munich's twin security gatherings, leaders warned that cyber conflict, transatlantic rifts and weaponised AI are pushing the rules-based order into a perilous transition, where deterrence falters, norms erode and digital sovereignty trumps multistakeholder ideals.
 A six year study of Global 2000 firms finds progress on email authentication but worrying gaps elsewhere. Despite rising DMARC adoption, falling DNS redundancy and uneven regional uptake leave companies exposed to domain based attacks.
A six year study of Global 2000 firms finds progress on email authentication but worrying gaps elsewhere. Despite rising DMARC adoption, falling DNS redundancy and uneven regional uptake leave companies exposed to domain based attacks.
 Poland thwarted a large-scale cyberattack on its energy grid without disruption, offering a rare case study in critical infrastructure resilience, decentralised energy governance, and the balancing act between openness and digital security.
Poland thwarted a large-scale cyberattack on its energy grid without disruption, offering a rare case study in critical infrastructure resilience, decentralised energy governance, and the balancing act between openness and digital security.
 Google's lawsuit against the Lighthouse phishing syndicate exposes the industrial scale of cybercrime, highlighting how criminals exploit easy access to digital infrastructure to scam millions. The broader supply chain enabling such operations demands urgent reform.
Google's lawsuit against the Lighthouse phishing syndicate exposes the industrial scale of cybercrime, highlighting how criminals exploit easy access to digital infrastructure to scam millions. The broader supply chain enabling such operations demands urgent reform.
 Cybercriminals live by the tenet "If it ain't broke, don't fix it." They'll use the same tactics repeatedly until they no longer work, then switch things up. That's why CISOs and their security teams maintain constant vigilance. Underscoring this, recent analysis of global DNS activity found that new domains continue to be a major tactic for bad actors.
Cybercriminals live by the tenet "If it ain't broke, don't fix it." They'll use the same tactics repeatedly until they no longer work, then switch things up. That's why CISOs and their security teams maintain constant vigilance. Underscoring this, recent analysis of global DNS activity found that new domains continue to be a major tactic for bad actors.
 Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks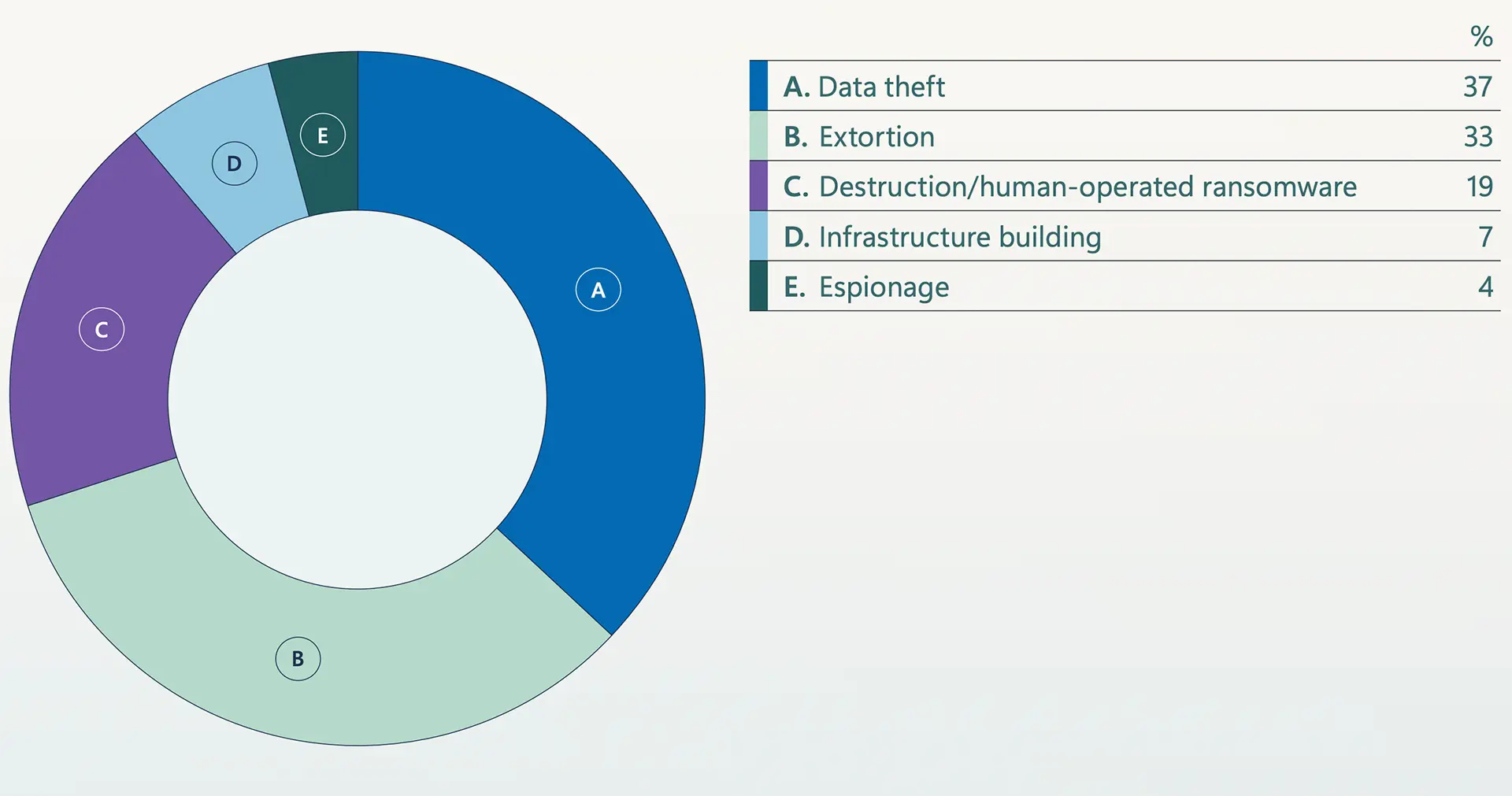 Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation
Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation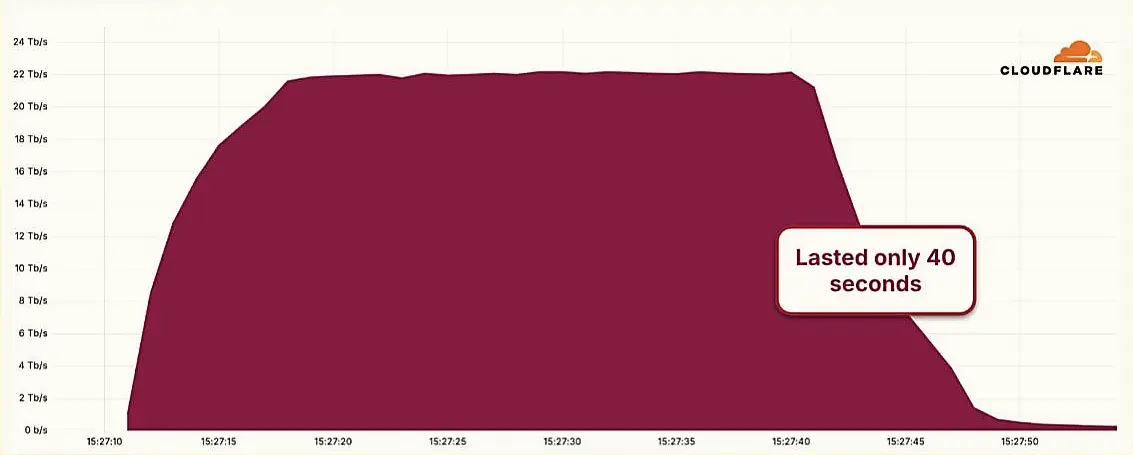 Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps
Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps European Airports Still Reeling from Ransomware Attack as Software Fix Nears
European Airports Still Reeling from Ransomware Attack as Software Fix Nears Chinese APT Groups Exploit Global Domains in Sweeping Cyber Campaign
Chinese APT Groups Exploit Global Domains in Sweeping Cyber Campaign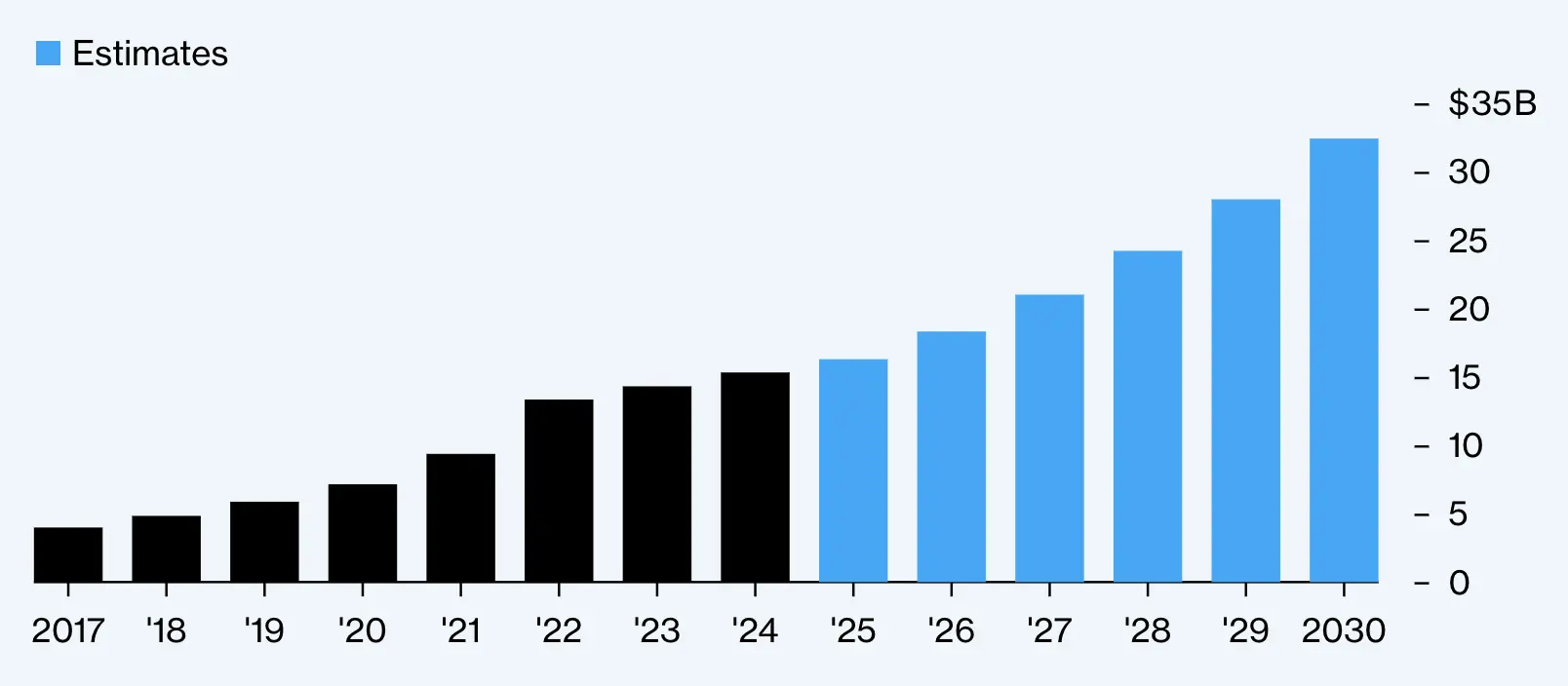 Cyberattacks Spur Boom in Insurance Demand Amid Rising Global Threats
Cyberattacks Spur Boom in Insurance Demand Amid Rising Global Threats Massive Iberian Power Outage Raises Cybersecurity Questions
Massive Iberian Power Outage Raises Cybersecurity Questions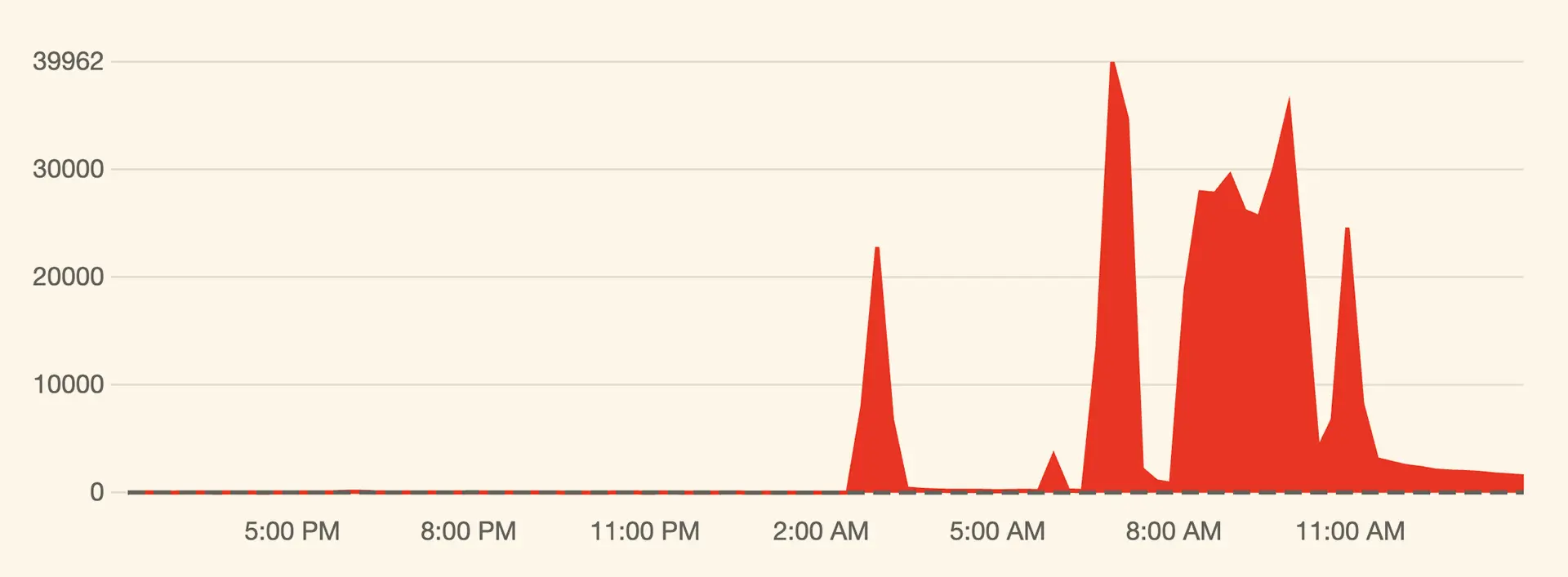 Massive Cyber Assault on X: Musk Hints at Foreign Involvement
Massive Cyber Assault on X: Musk Hints at Foreign Involvement Chinese Hackers Exploit U.S. Telecom Systems, Eviction Efforts Lag
Chinese Hackers Exploit U.S. Telecom Systems, Eviction Efforts Lag Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals
Chinese Hackers Had Access to Canadian Government Systems for Years, Report Reveals Sudanese Nationals Charged in Global Cyberattack Campaign
Sudanese Nationals Charged in Global Cyberattack Campaign Over 2 Million VPN Passwords Compromised by Malware Attacks
Over 2 Million VPN Passwords Compromised by Malware Attacks FBI Takes Down China-Backed Botnet, Facilitates Ransomware Negotiations
FBI Takes Down China-Backed Botnet, Facilitates Ransomware Negotiations Mystery Malware Takes Down 600,000 Windstream Routers in Coordinated Attack
Mystery Malware Takes Down 600,000 Windstream Routers in Coordinated Attack