

 Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
Geofeed data, long reliant on unverifiable self-assertions, faces mounting security risks. Integrating RPKI could transform it into a trusted, cryptographically validated infrastructure, strengthening routing integrity, regulatory compliance, and digital sovereignty across an increasingly contested internet.
 Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
Unicorn firms lead in DNS-based security adoption, signaling technical maturity, while Global 2000 rely on enterprise registrars. Gaps in redundancy and brand protection expose supply chain risks as cyberattacks intensify across industries globally today.
 Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
 Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
Africa's looming AI rules expose a deeper problem: foreign-controlled infrastructure, weak enforcement capacity and externally governed data flows are eroding digital sovereignty, leaving states unable to regulate, protect citizens or meet global obligations.
 A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
A flawed abuse-response system shifts costs from perpetrators to intermediaries, overwhelming enforcement. The Trusted Notifier Network seeks to realign incentives, curb low-quality reporting, and restore efficiency by embedding trust, accountability, and cost redistribution.
 Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
 A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
 Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
 Poland thwarted a large-scale cyberattack on its energy grid without disruption, offering a rare case study in critical infrastructure resilience, decentralised energy governance, and the balancing act between openness and digital security.
Poland thwarted a large-scale cyberattack on its energy grid without disruption, offering a rare case study in critical infrastructure resilience, decentralised energy governance, and the balancing act between openness and digital security.
 eco's topDNS initiative and AV-Test are publishing monthly reports to help ISPs detect and mitigate DNS abuse by analysing malware, phishing, and PUA trends, creating a long-term data foundation for industry-wide transparency.
eco's topDNS initiative and AV-Test are publishing monthly reports to help ISPs detect and mitigate DNS abuse by analysing malware, phishing, and PUA trends, creating a long-term data foundation for industry-wide transparency.
 Cybercriminals live by the tenet "If it ain't broke, don't fix it." They'll use the same tactics repeatedly until they no longer work, then switch things up. That's why CISOs and their security teams maintain constant vigilance. Underscoring this, recent analysis of global DNS activity found that new domains continue to be a major tactic for bad actors.
Cybercriminals live by the tenet "If it ain't broke, don't fix it." They'll use the same tactics repeatedly until they no longer work, then switch things up. That's why CISOs and their security teams maintain constant vigilance. Underscoring this, recent analysis of global DNS activity found that new domains continue to be a major tactic for bad actors.
 Satellites make it possible for governments to provide essential services, such as national defense, navigation, and weather forecasting. Private ventures use satellites to offer highly desired services that include video program distribution, telecommunications, and Internet access. The Russian launch of a satellite, with nuclear power and the likely ability to disable satellites, underscores how satellites are quite vulnerable to both natural and manmade ruin.
Satellites make it possible for governments to provide essential services, such as national defense, navigation, and weather forecasting. Private ventures use satellites to offer highly desired services that include video program distribution, telecommunications, and Internet access. The Russian launch of a satellite, with nuclear power and the likely ability to disable satellites, underscores how satellites are quite vulnerable to both natural and manmade ruin.
 In this article, I present an overview of a series of 'proof-of-concept' studies looking at the application of domain-name entropy as a means of clustering together related domain registrations, and serving as an input into potential metrics to determine the likely level of threat which may be posed by a domain.
In this article, I present an overview of a series of 'proof-of-concept' studies looking at the application of domain-name entropy as a means of clustering together related domain registrations, and serving as an input into potential metrics to determine the likely level of threat which may be posed by a domain.
 OpenXDR is one of the most cost-effective SIEM alternatives that help businesses detect and mitigate threats within hectic modern architectures. A single cyber incident impacts every aspect of a business -- from system downtime, revenue losses, and reputation damage to disrupted operations.
OpenXDR is one of the most cost-effective SIEM alternatives that help businesses detect and mitigate threats within hectic modern architectures. A single cyber incident impacts every aspect of a business -- from system downtime, revenue losses, and reputation damage to disrupted operations.
 While threat actors can use any domain across thousands of top-level domains (TLDs), they often have favorites. For instance, you may be familiar with Spamhaus's 10 most-abused TLDs for spamming. WhoisXML API researchers recently built on this list by analyzing 40,000 newly registered domains (NRDs) that sported some of the listed unreputable TLDs. We called this study "DNS Abuse Trends: Dissecting the Domains Under the Most-Abused TLDs."
While threat actors can use any domain across thousands of top-level domains (TLDs), they often have favorites. For instance, you may be familiar with Spamhaus's 10 most-abused TLDs for spamming. WhoisXML API researchers recently built on this list by analyzing 40,000 newly registered domains (NRDs) that sported some of the listed unreputable TLDs. We called this study "DNS Abuse Trends: Dissecting the Domains Under the Most-Abused TLDs."
 Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Backlash Over Potential Firing of U.S. Election Cybersecurity’s Top Official
Backlash Over Potential Firing of U.S. Election Cybersecurity’s Top Official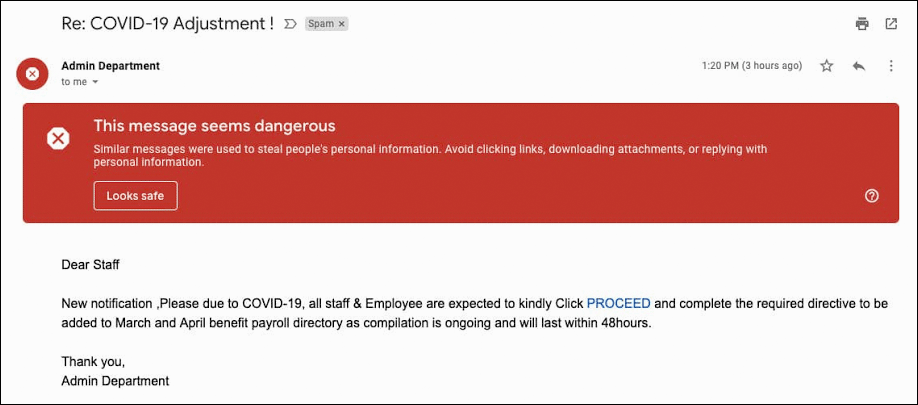 Google Reports 18 Million Daily COVID-19 Related Malware, Phishing Emails Per Day
Google Reports 18 Million Daily COVID-19 Related Malware, Phishing Emails Per Day Zoom Faces Class-Action Lawsuit, Accused of Overstating Its Privacy Standards
Zoom Faces Class-Action Lawsuit, Accused of Overstating Its Privacy Standards