

Cybersecurity |
Sponsored by |

|
 Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
Threat intelligence is shifting from a passive feed to a core operational layer, helping infrastructure defenders connect fragmented signals, identify recurring attack patterns, and prioritise responses in an increasingly modular and fast-moving cybercrime ecosystem.
 A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
A once-trusted internet protocol is showing its age. DNSXplore, a global DNSSEC archive, exposes weaknesses, improves diagnostics and nudges adoption, helping secure the cryptographic chain underpinning online trust.
 As IP addresses move across borders, outdated geolocation guesses cause service failures and regulatory risks. Geofeed and Signed Geofeed replace inference with verified declarations, promising accurate, resilient and sovereign foundations for global internet infrastructure governance.
As IP addresses move across borders, outdated geolocation guesses cause service failures and regulatory risks. Geofeed and Signed Geofeed replace inference with verified declarations, promising accurate, resilient and sovereign foundations for global internet infrastructure governance.
 The FCC warns telecom companies of rising ransomware threats after attacks quadrupled since 2022. The agency urges stronger defenses including patching, multifactor authentication, network segmentation, and closer oversight of vendors and incident response planning.
The FCC warns telecom companies of rising ransomware threats after attacks quadrupled since 2022. The agency urges stronger defenses including patching, multifactor authentication, network segmentation, and closer oversight of vendors and incident response planning.
 Iran's near-total internet blackout during airstrikes reveals how cyberattacks, sanctions and platform power can isolate a nation. The conflict shows digital infrastructure, satellites and cloud services becoming decisive weapons in modern geopolitical competition worldwide today.
Iran's near-total internet blackout during airstrikes reveals how cyberattacks, sanctions and platform power can isolate a nation. The conflict shows digital infrastructure, satellites and cloud services becoming decisive weapons in modern geopolitical competition worldwide today.
 Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
Bad actors are exploiting DNS with growing sophistication. New domains dominate threat infrastructure, daily user exposures are rising, and AI is accelerating attack creation, making DNS intelligence an increasingly critical early-warning system for modern cyber defence.
 Generative AI has turned brand impersonation from a nuisance into an industrial-scale threat, eroding trust. As ICANN's 2026 round approaches, DotBrand domains promise a structural fix to spoofing that strategies failed to deliver in 2012.
Generative AI has turned brand impersonation from a nuisance into an industrial-scale threat, eroding trust. As ICANN's 2026 round approaches, DotBrand domains promise a structural fix to spoofing that strategies failed to deliver in 2012.
 At Munich's twin security gatherings, leaders warned that cyber conflict, transatlantic rifts and weaponised AI are pushing the rules-based order into a perilous transition, where deterrence falters, norms erode and digital sovereignty trumps multistakeholder ideals.
At Munich's twin security gatherings, leaders warned that cyber conflict, transatlantic rifts and weaponised AI are pushing the rules-based order into a perilous transition, where deterrence falters, norms erode and digital sovereignty trumps multistakeholder ideals.
 A six year study of Global 2000 firms finds progress on email authentication but worrying gaps elsewhere. Despite rising DMARC adoption, falling DNS redundancy and uneven regional uptake leave companies exposed to domain based attacks.
A six year study of Global 2000 firms finds progress on email authentication but worrying gaps elsewhere. Despite rising DMARC adoption, falling DNS redundancy and uneven regional uptake leave companies exposed to domain based attacks.
 ICANN invites proposals for its DNSSEC and Security Workshop at the ICANN85 Community Forum in March 2026, offering a platform for global experts to share insights on DNS, routing security, and emerging threats.
ICANN invites proposals for its DNSSEC and Security Workshop at the ICANN85 Community Forum in March 2026, offering a platform for global experts to share insights on DNS, routing security, and emerging threats.
 A 2026 outlook charts Internet governance between fear and hope, tracking cyber conflict, digital trade and taxation, shrinking rights, and global AI rivalry, while asking whether multistakeholder cooperation can still steer the network toward stability.
A 2026 outlook charts Internet governance between fear and hope, tracking cyber conflict, digital trade and taxation, shrinking rights, and global AI rivalry, while asking whether multistakeholder cooperation can still steer the network toward stability.
 Internet governance is shifting from participatory forums to security-driven mandates. As authority accelerates ahead of legitimacy, technical systems face growing instability and operators absorb the risks of politically motivated control.
Internet governance is shifting from participatory forums to security-driven mandates. As authority accelerates ahead of legitimacy, technical systems face growing instability and operators absorb the risks of politically motivated control.
 As Internet governance fragments in 2026, authority shifts from open, multistakeholder forums to state-led security regimes, legal instruments, and alliance-based cooperation, challenging longstanding institutions and reshaping global norms through enforcement rather than consensus.
As Internet governance fragments in 2026, authority shifts from open, multistakeholder forums to state-led security regimes, legal instruments, and alliance-based cooperation, challenging longstanding institutions and reshaping global norms through enforcement rather than consensus.
 Despite deep geopolitical divides, the WSIS+20 outcome document was adopted by consensus, preserving a multistakeholder vision for the digital future while deferring controversial issues to a time more conducive to progress.
Despite deep geopolitical divides, the WSIS+20 outcome document was adopted by consensus, preserving a multistakeholder vision for the digital future while deferring controversial issues to a time more conducive to progress.
 The ICC's new cyber policy reframes Internet infrastructure as crucial to prosecuting atrocities, prompting DNS operators and network providers to grapple with emerging obligations around evidence, neutrality, and cooperation in international justice.
The ICC's new cyber policy reframes Internet infrastructure as crucial to prosecuting atrocities, prompting DNS operators and network providers to grapple with emerging obligations around evidence, neutrality, and cooperation in international justice.
 U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Iran Expands Digital Dragnet After Crushing Protests
Iran Expands Digital Dragnet After Crushing Protests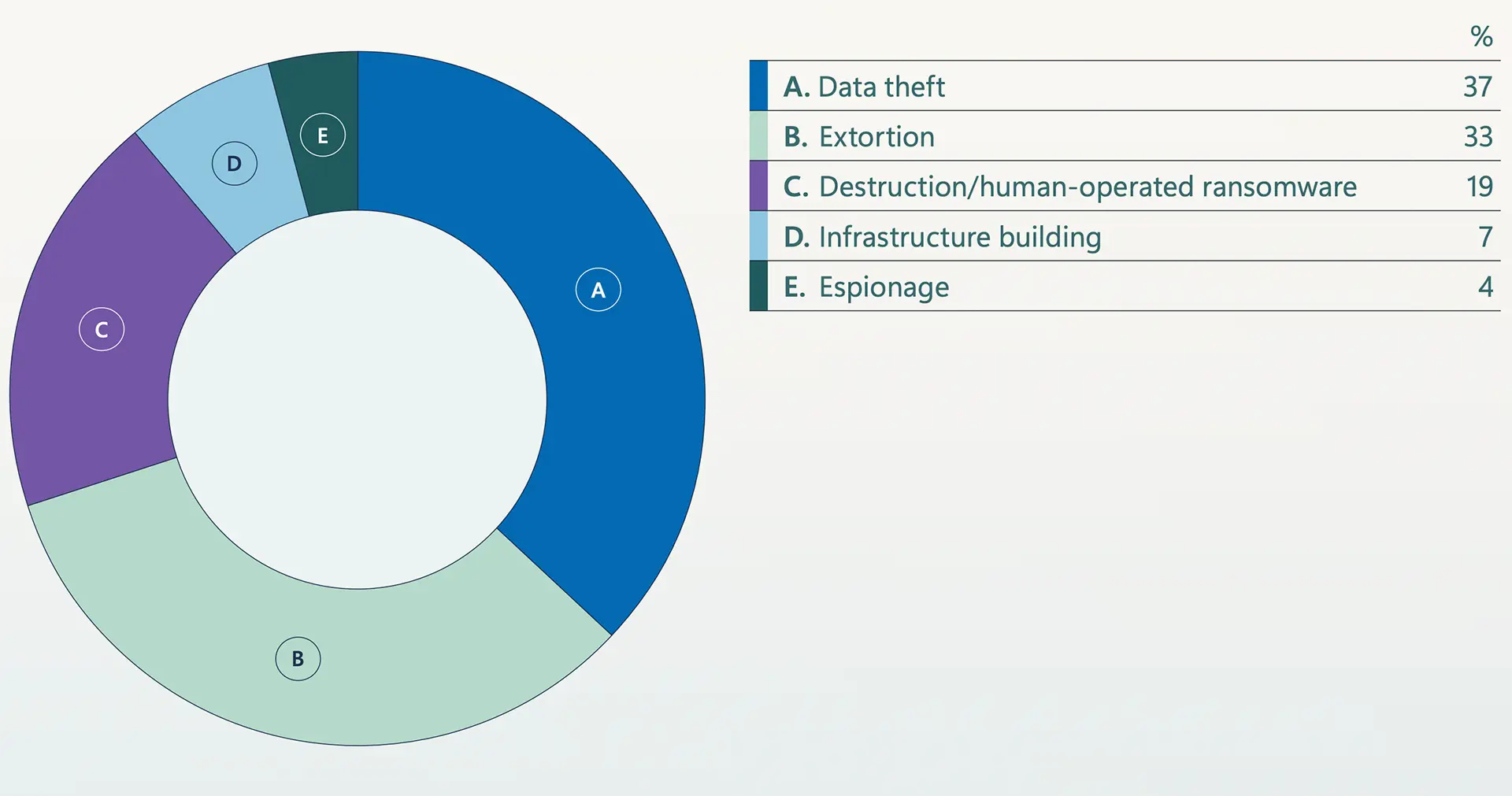 Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation
Microsoft Warns Extortion Drives Majority of Attacks Amid AI Escalation, Identity Collapse, and Global Fragmentation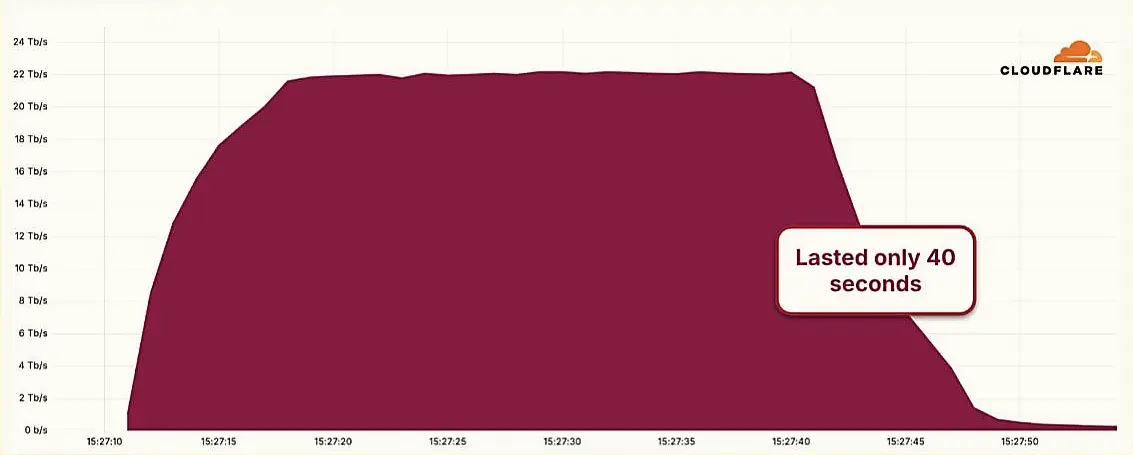 Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps
Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps European Airports Still Reeling from Ransomware Attack as Software Fix Nears
European Airports Still Reeling from Ransomware Attack as Software Fix Nears Chinese APT Groups Exploit Global Domains in Sweeping Cyber Campaign
Chinese APT Groups Exploit Global Domains in Sweeping Cyber Campaign Advanced AI Is Reshaping the Cybercriminal Landscape at Alarming Speed
Advanced AI Is Reshaping the Cybercriminal Landscape at Alarming Speed FTC to Big Tech: Don’t Trade American Privacy for Foreign Demands
FTC to Big Tech: Don’t Trade American Privacy for Foreign Demands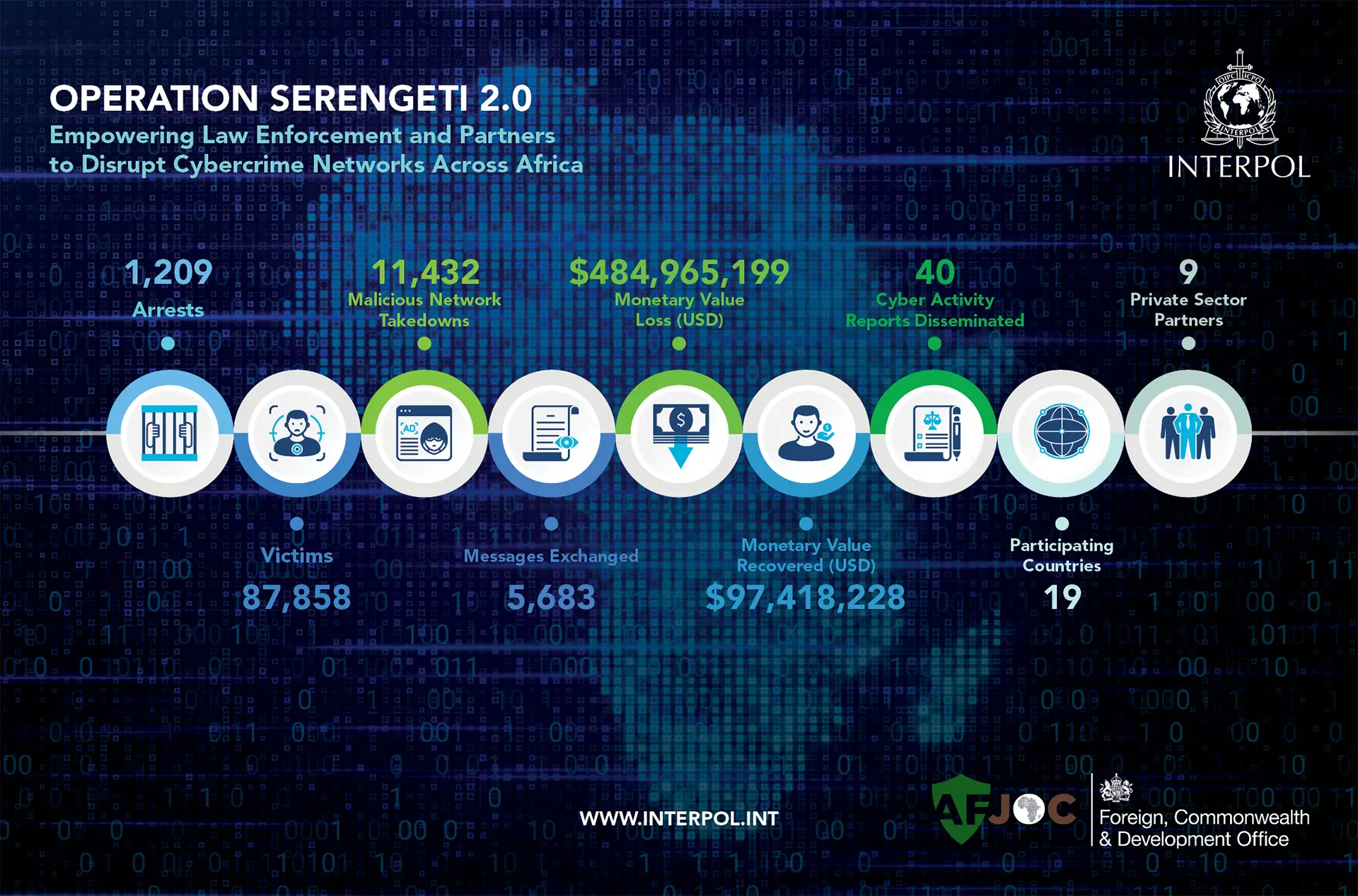 INTERPOL Leads Arrest of 1,209 Suspects in Pan-African Cybercrime Crackdown, Recovers $97 Million
INTERPOL Leads Arrest of 1,209 Suspects in Pan-African Cybercrime Crackdown, Recovers $97 MillionAddressing DNS abuse and maintaining a healthy DNS ecosystem are important components of Verisign's commitment to being a responsible steward of the internet. We continuously engage with the Internet Corporation for Assigned Names and Numbers (ICANN) and other industry partners to help ensure the secure, stable and resilient operation of the DNS. more
Verisign just released its Q2 2018 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of customers of Verisign DDoS Protection Services. more
Currently scheduled for October 11, 2018, the Internet Corporation for Assigned Names and Numbers (ICANN) plans to change the cryptographic key that helps to secure the internet's Domain Name System (DNS) by performing a Root Zone Domain Name System Security Extensions (DNSSEC) key signing key (KSK) rollover. more
Verisign has released its Q1 2018 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of Verisign DDoS Protection Services, and security research conducted by Verisign Security Services. more
As DNS attacks grow in frequency and impact, organizations can no longer afford to overlook DNS security as part of their overall defense-in-depth strategy. As with IT security in general, no single tactic can address the entire DNS threat landscape or secure the complete DNS ecosystem. more
Verisign has released its Q4 2017 DDoS Trends Report, which represents a unique view into the attack trends unfolding online, through observations and insights derived from distributed denial of service (DDoS) attack mitigations enacted on behalf of Verisign DDoS Protection Services and security research conducted by Verisign Security Services. more
Cybercriminals recognize the value of DNS availability and look for ways to compromise DNS uptime and the DNS servers that support it. As such, DNS becomes an important point of security enforcement and a potential point in the Cyber Kill Chain for many cyber-attacks. more