

 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
 Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
 ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
 As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
 The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
 Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
 An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
An official-looking renewal notice reveals how open namespaces shift verification burdens onto users. Restricted government domains like .gov.au function as trust infrastructure, embedding authority into the namespace and reducing fraud, confusion, and verification costs.
 Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
Mounting signs of consumer distress, from unpaid utility bills to rising loan delinquencies, are raising uncomfortable questions for internet providers about whether broadband remains recession-proof as households increasingly trade home connections for cheaper wireless alternatives.
 ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
ICANN's Smart Africa engagement shows how proposals can gain authority without formal endorsement, raising harder questions about CAIGA, ICP-2 and whether regional partnerships need earlier safeguards when RIR governance begins to shift under institutional cover.
 As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
As cross-border cyber enforcement falters, critics argue Article 19's DNS abuse framework prioritizes procedural purity over user protection, leaving courts too slow to counter AI-driven phishing, rapid-flux domains, and increasingly automated online threats.
 As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
As Africa digitises rapidly, control over data is emerging as a strategic contest. Foreign infrastructure dominance exposes economic and cybersecurity vulnerabilities, pushing governments to prioritise digital capability, regional cooperation, and stronger sovereignty over the systems powering the continent's future.
 An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
An ICANN-backed African internet-governance initiative exposed a deeper institutional problem: whether global coordinators must warn when regional policy processes drift into RIR governance, before facilitation, silence and funding harden into implied legitimacy for contested reforms.
 Iran Begins Restoring Internet After Record 88-Day Blackout
Iran Begins Restoring Internet After Record 88-Day Blackout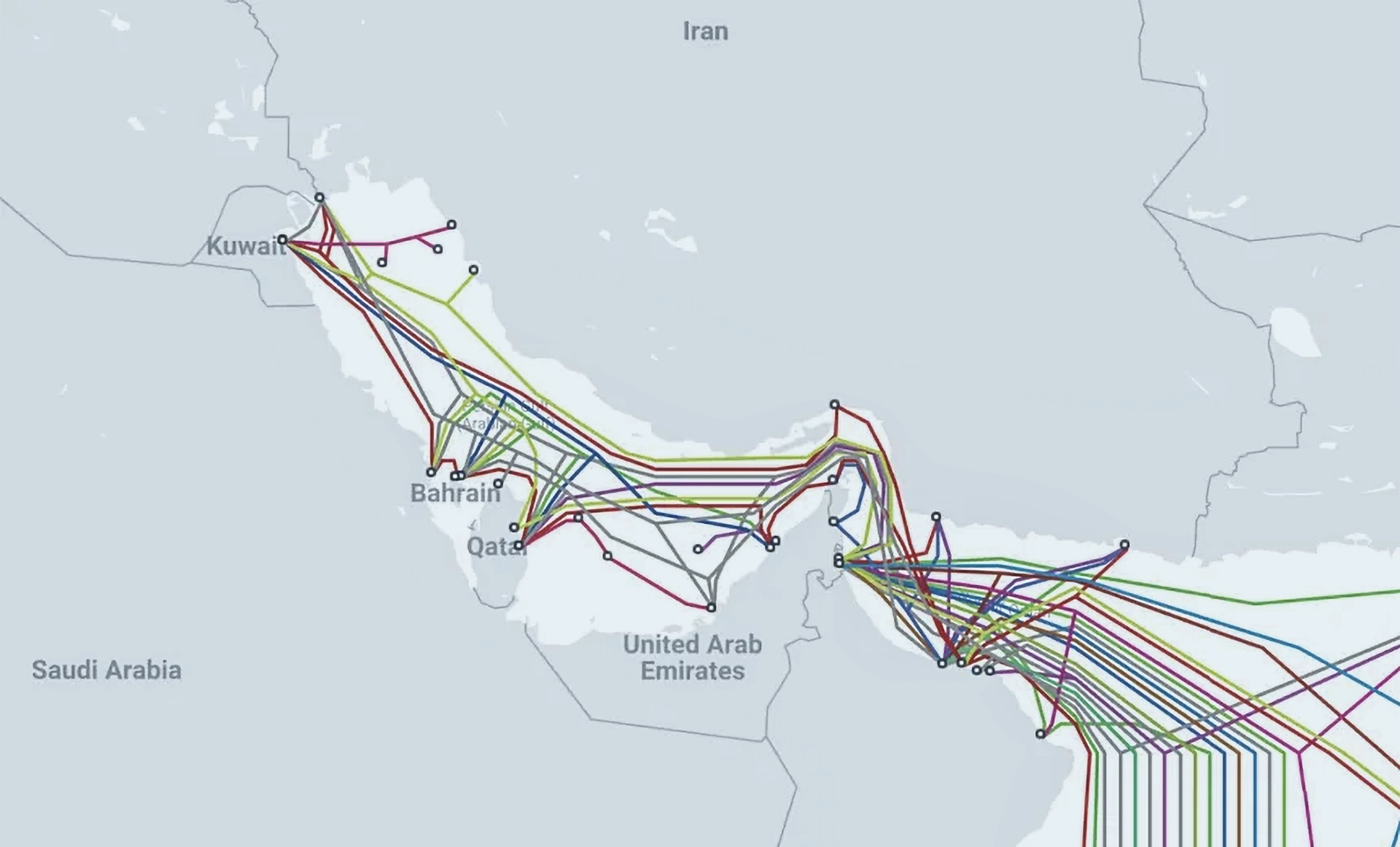 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts
ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts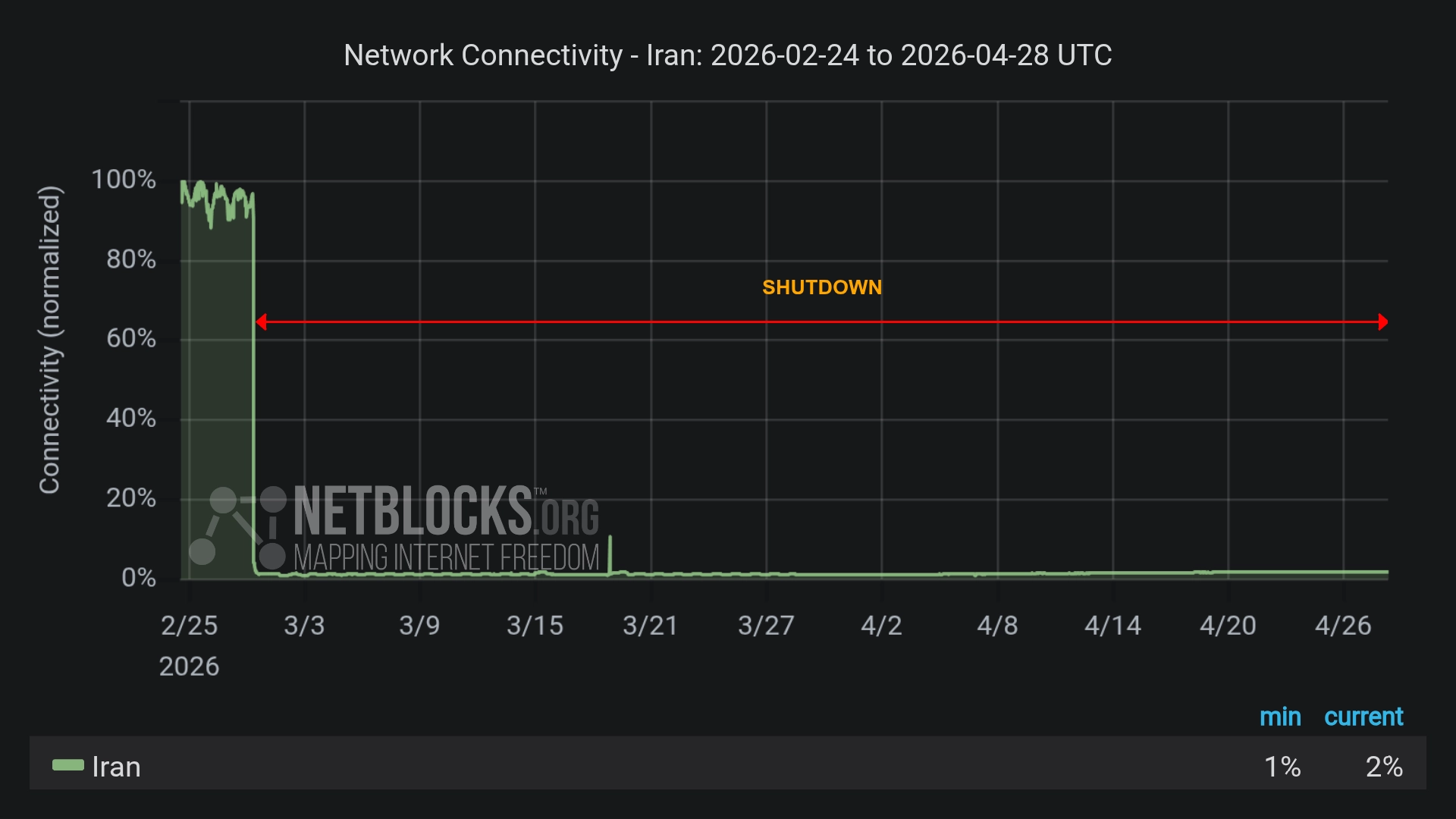 Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Iranians Outsmart Internet Blackout to Broadcast Airstrikes
Iranians Outsmart Internet Blackout to Broadcast Airstrikes Iran Expands Digital Dragnet After Crushing Protests
Iran Expands Digital Dragnet After Crushing Protests David J. Farber, Early Architect of the Internet, Dies at 91
David J. Farber, Early Architect of the Internet, Dies at 91