

 Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
Africa's cybersecurity failures stem less from sophisticated hackers than from insecure system design, weak governance and limited skills, leaving institutions exposed and shifting the challenge from external threats to internal accountability and resilience.
I'm writing this from Taipei, where I have lived in peace for over 10 years. Sadly I learned that during this week, intermediate-range ballistic missiles (operated by China) have flown far above the capital of Taiwan and that five of them have landed in the waters of Japan's exclusive economic zone (EEZ). This provocative live-firing drill came as a direct response from China following Pelosi's visit.
 In light of the Biden administration's recent efforts in protecting critical infrastructure from cyber threats, new research from CSC indicates that a majority of the top energy companies in the U.S. are vulnerable to attack due to shortcomings in their online operations. Specifically, these organizations are vulnerable to domain name and domain name system (DNS) hijacking and phishing attacks based on their lack of effective domain security.
In light of the Biden administration's recent efforts in protecting critical infrastructure from cyber threats, new research from CSC indicates that a majority of the top energy companies in the U.S. are vulnerable to attack due to shortcomings in their online operations. Specifically, these organizations are vulnerable to domain name and domain name system (DNS) hijacking and phishing attacks based on their lack of effective domain security.
 The term "attack surface" is often heard in cybersecurity conversations. It refers to the sum of all possible attack vectors or the vulnerabilities that threat actors can exploit to penetrate a target network or damage an organization somehow. An unused and forgotten subdomain, for instance, can become an attack vector when taken over. Certain categories of companies have very large attack surfaces. Such is the case of streaming media businesses like Netflix and HBO Max.
The term "attack surface" is often heard in cybersecurity conversations. It refers to the sum of all possible attack vectors or the vulnerabilities that threat actors can exploit to penetrate a target network or damage an organization somehow. An unused and forgotten subdomain, for instance, can become an attack vector when taken over. Certain categories of companies have very large attack surfaces. Such is the case of streaming media businesses like Netflix and HBO Max.
 As outlined in CSC's recent 2020 Domain Security Report: Forbes Global 2000 Companies, cybercriminals are disrupting organizations by attacking the protocol responsible for their online presence -- their domain name system (DNS). When a DNS is overwhelmed with traffic due to a distributed denial of service (DDoS) attack or configuration error, content and applications become inaccessible to users, affecting both revenue and reputation.
As outlined in CSC's recent 2020 Domain Security Report: Forbes Global 2000 Companies, cybercriminals are disrupting organizations by attacking the protocol responsible for their online presence -- their domain name system (DNS). When a DNS is overwhelmed with traffic due to a distributed denial of service (DDoS) attack or configuration error, content and applications become inaccessible to users, affecting both revenue and reputation.
 The evolution of the internet is anchored in the phenomenon of new technologies replacing their older counterparts. But technology evolution can be just as much about building upon what is already in place, as it is about tearing down past innovations. Indeed, the emergence of cloud computing has been powered by extending an unlikely underlying component: the more than 30-year-old global Domain Name System (DNS).
The evolution of the internet is anchored in the phenomenon of new technologies replacing their older counterparts. But technology evolution can be just as much about building upon what is already in place, as it is about tearing down past innovations. Indeed, the emergence of cloud computing has been powered by extending an unlikely underlying component: the more than 30-year-old global Domain Name System (DNS).
 Nokia Deepfield is another company that works in the background on the web, and that analyzes data traffic patterns for the big ISPs. Their June 4 report on web traffic reports about the same thing we're hearing from most large ISPs -- the volume of web traffic suddenly shot up since the onset of the pandemic. Nokia Deepfield says that the increase in traffic has settled in at about a 25% increase over pre-COVID levels.
Nokia Deepfield is another company that works in the background on the web, and that analyzes data traffic patterns for the big ISPs. Their June 4 report on web traffic reports about the same thing we're hearing from most large ISPs -- the volume of web traffic suddenly shot up since the onset of the pandemic. Nokia Deepfield says that the increase in traffic has settled in at about a 25% increase over pre-COVID levels.
 The domain name system (DNS) grew to prominence during the initial, innocent days of the internet. During that time, early internet users tended to work for government or education organizations where trust was assumed, and security was not even a consideration. Since the online community was small and the internet was sparsely used, the importance of DNS was not widely understood, and as a consequence, left undefended.
The domain name system (DNS) grew to prominence during the initial, innocent days of the internet. During that time, early internet users tended to work for government or education organizations where trust was assumed, and security was not even a consideration. Since the online community was small and the internet was sparsely used, the importance of DNS was not widely understood, and as a consequence, left undefended.
 Last week an ICANN registrar, Namejuice, went off the air for the better part of the day -- disappearing off the internet at approximately 8:30 am, taking all domains delegated to its nameservers with it, and did not come back online until close to 11 pm ET. That was a full business day and more of complete outage for all businesses, domains, websites, and email who were using the Namejuice nameservers -- something many of them were doing.
Last week an ICANN registrar, Namejuice, went off the air for the better part of the day -- disappearing off the internet at approximately 8:30 am, taking all domains delegated to its nameservers with it, and did not come back online until close to 11 pm ET. That was a full business day and more of complete outage for all businesses, domains, websites, and email who were using the Namejuice nameservers -- something many of them were doing.
 In October of 2016 the Mirai botnet came thundering onto the internet landscape. A digital Godzilla, a DDoS King Kong, this Internet of Things-powered behemoth began smashing DDoS attack records, online powerhouses like Reddit, Etsy, Spotify, CNN and the New York Times crumbling under its fists. When the dust had settled, and services had been restored, one thing seemed certain: a new era of DDoS attacks was upon us. Mirai was terrifying as a botnet but even worse as a harbinger.
In October of 2016 the Mirai botnet came thundering onto the internet landscape. A digital Godzilla, a DDoS King Kong, this Internet of Things-powered behemoth began smashing DDoS attack records, online powerhouses like Reddit, Etsy, Spotify, CNN and the New York Times crumbling under its fists. When the dust had settled, and services had been restored, one thing seemed certain: a new era of DDoS attacks was upon us. Mirai was terrifying as a botnet but even worse as a harbinger.
 Reflection amplification is a technique that allows cyber attackers to both magnify the amount of malicious traffic they can generate, and obfuscate the sources of that attack traffic. For the past five years, this combination has been irresistible to attackers, and for good reason. This simple capability, of turning small requests into larger, 'amplified' responses, changed the Distributed Denial of Service (DDoS) attack landscape dramatically.
Reflection amplification is a technique that allows cyber attackers to both magnify the amount of malicious traffic they can generate, and obfuscate the sources of that attack traffic. For the past five years, this combination has been irresistible to attackers, and for good reason. This simple capability, of turning small requests into larger, 'amplified' responses, changed the Distributed Denial of Service (DDoS) attack landscape dramatically.
It is once again time for our annual review of posts that received the most attention on CircleID during the past year. Congratulations to all the 2017 participants for sharing their thoughts and making a difference in the industry. 2017 marked CircleID's 15th year of operation as a medium dedicated to all critical matters related to the Internet infrastructure and services. We are in the midst of historic times, facing rapid technological developments and there is a lot to look forward to in 2018.
 The Mirai DDOS attack happened just over a year ago, on the 21st October 2016. The attack was certainly a major landmark regarding the sorry history of "landmark" DDOS attacks on the Internet. It's up there with the Morris Worm of 1988, Slammer of 2002, Sapphine/Slammer of 2009 and of course Conficker in 2008. What made the Mirai attack so special?
The Mirai DDOS attack happened just over a year ago, on the 21st October 2016. The attack was certainly a major landmark regarding the sorry history of "landmark" DDOS attacks on the Internet. It's up there with the Morris Worm of 1988, Slammer of 2002, Sapphine/Slammer of 2009 and of course Conficker in 2008. What made the Mirai attack so special?
 Building IoT ventures from scratch by prototyping hardware devices and their backend systems as well as working for a large company that tries to sell IoT devices itself, we learned a lot about the pitfalls and problems concerning security in the IoT. Nearly every connected device out there proved to be vulnerable to attacks. Researchers showed that it's possible to remotely take control over autonomous vehicles, implanted medical devices were manipulated, voting machines compromised and of course all sorts of other "smart" devices...
Building IoT ventures from scratch by prototyping hardware devices and their backend systems as well as working for a large company that tries to sell IoT devices itself, we learned a lot about the pitfalls and problems concerning security in the IoT. Nearly every connected device out there proved to be vulnerable to attacks. Researchers showed that it's possible to remotely take control over autonomous vehicles, implanted medical devices were manipulated, voting machines compromised and of course all sorts of other "smart" devices...
Back in the early 2000s, several notable Internet researchers were predicting the death of the Internet. Based on the narrative, the Internet infrastructure had not been designed for the scale that was being projected at the time, supposedly leading to fatal security and scalability issues. Yet somehow the Internet industry has always found a way to dodge the bullet at the very last minute.
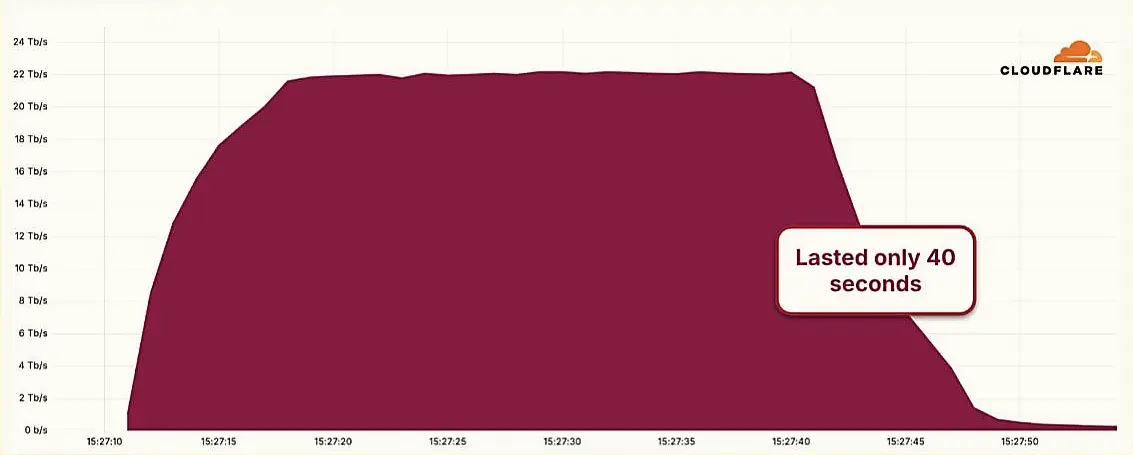 Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps
Hyper-Volumetric DDoS Attack Sets New Benchmark at 22.2 Tbps Sudanese Nationals Charged in Global Cyberattack Campaign
Sudanese Nationals Charged in Global Cyberattack Campaign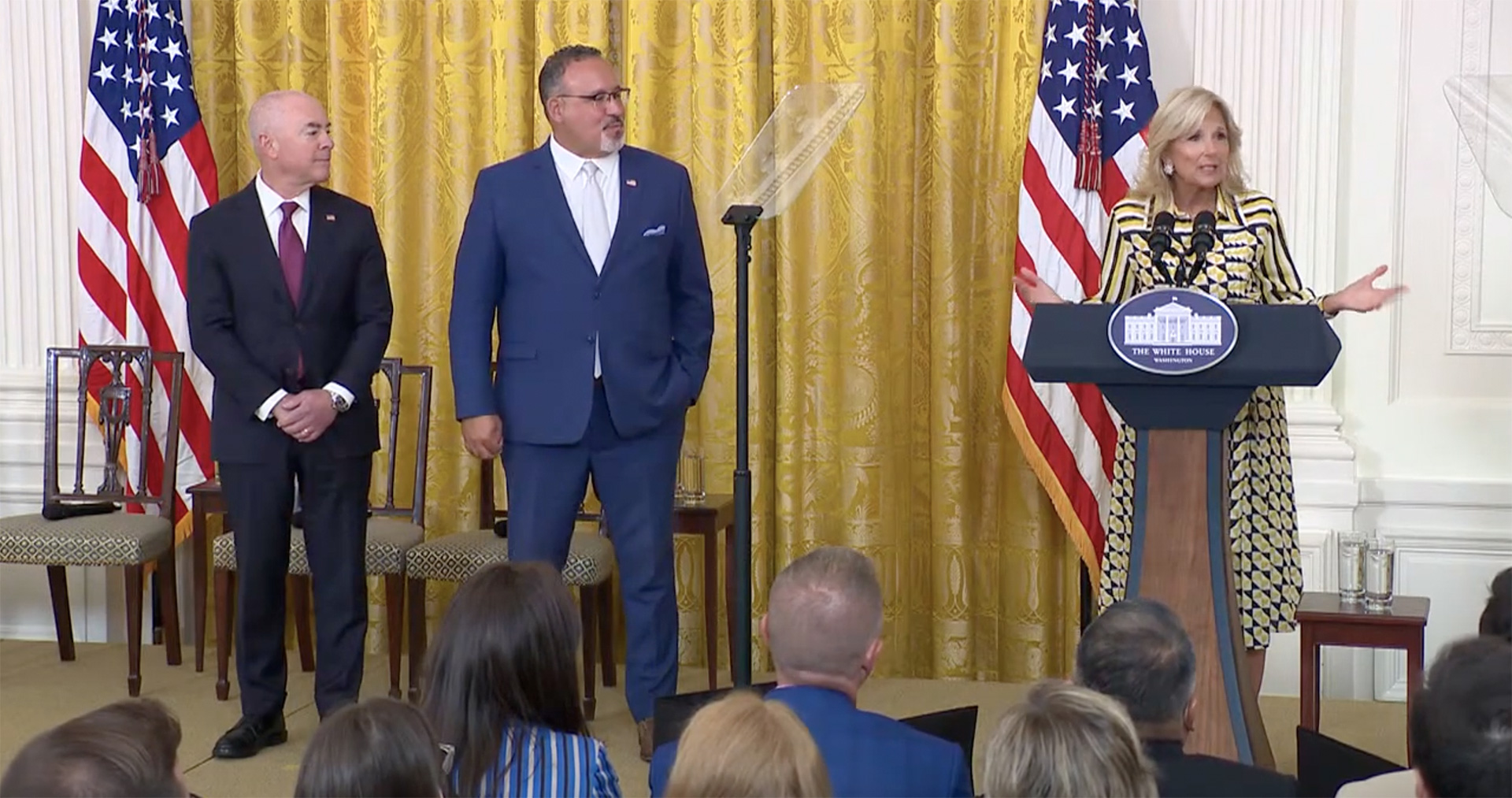 U.S. Schools Targeted in Ransomware Attacks: White House Responds
U.S. Schools Targeted in Ransomware Attacks: White House Responds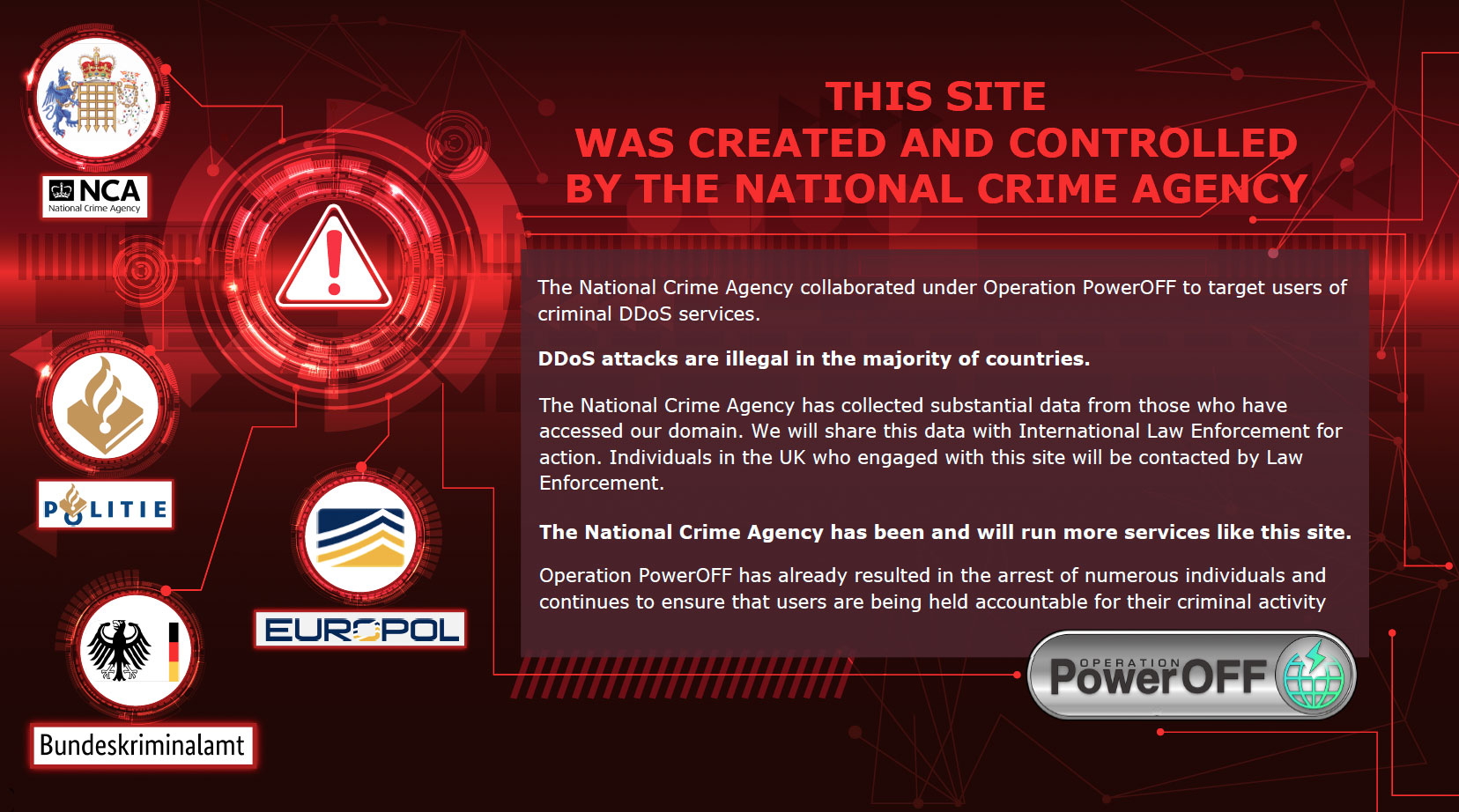 NCA Launches Campaign to Curb DDoS-for-Hire Website Use, Warns of Legal Risks
NCA Launches Campaign to Curb DDoS-for-Hire Website Use, Warns of Legal Risks Petya Ransomware Spreading Rapidly Worldwide, Effecting Banks, Telecom, Businesses, Power Companies
Petya Ransomware Spreading Rapidly Worldwide, Effecting Banks, Telecom, Businesses, Power Companies