

 As ICANN confronts a harsher geopolitical era, its long-delayed review of the UDRP has become a defining test of whether the multistakeholder model can still deliver legitimate, effective Internet governance and sustain confidence in its future.
As ICANN confronts a harsher geopolitical era, its long-delayed review of the UDRP has become a defining test of whether the multistakeholder model can still deliver legitimate, effective Internet governance and sustain confidence in its future.
 Canada's online pharmacy industry is urging a ban on unregulated peptide sales, warning that products marketed for weight loss, bodybuilding and other uses pose serious health risks, evade regulatory oversight, and are increasingly sold online without prescriptions.
Canada's online pharmacy industry is urging a ban on unregulated peptide sales, warning that products marketed for weight loss, bodybuilding and other uses pose serious health risks, evade regulatory oversight, and are increasingly sold online without prescriptions.
 Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
Domains and DNS underpin modern business operations, yet security gaps remain widespread. CSC's latest research shows why stronger domain protections are essential to resilience, helping companies reduce disruption, safeguard trust, and maintain continuity when attacks strike.
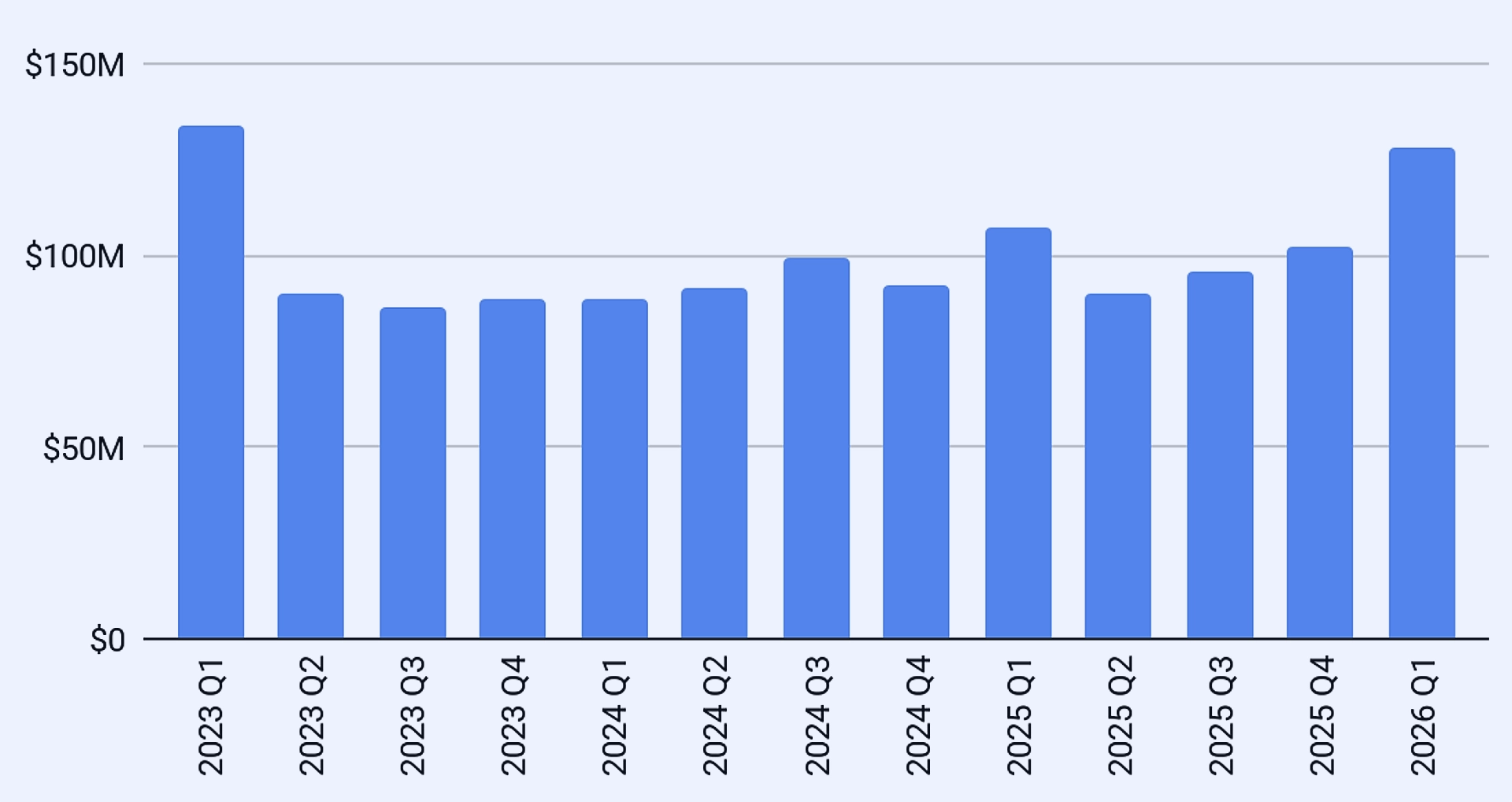
 After two years of falling prices, the IPv4 market has turned decisively. Surging transfer volumes, AI infrastructure demand and looming broadband expansion are tightening supply, pushing prices higher and leaving patient buyers facing a costlier reality.
After two years of falling prices, the IPv4 market has turned decisively. Surging transfer volumes, AI infrastructure demand and looming broadband expansion are tightening supply, pushing prices higher and leaving patient buyers facing a costlier reality.
 As the UN turns to AI governance, old lessons from internet governance loom large: multistakeholder rules matter, but sharper risks, geopolitical rivalry and machine autonomy make consensus harder and more urgent than before for all.
As the UN turns to AI governance, old lessons from internet governance loom large: multistakeholder rules matter, but sharper risks, geopolitical rivalry and machine autonomy make consensus harder and more urgent than before for all.
 Africa's data sovereignty debate focuses too heavily on where information is stored. Real sovereignty depends on control of cloud platforms, encryption, identity systems, and critical digital infrastructure that determine resilience, autonomy, and strategic power.
Africa's data sovereignty debate focuses too heavily on where information is stored. Real sovereignty depends on control of cloud platforms, encryption, identity systems, and critical digital infrastructure that determine resilience, autonomy, and strategic power.
 New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
New data on DNS abuse reveals most malicious domains remain active beyond 24 hours, while a handful of registrars host the bulk of infrastructure, leaving India's population of first-generation internet users uniquely exposed to fraud.
 As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
As AI agents automate phishing, impersonation and domain abuse at machine scale, the Brand Registry Group argues that dotBrand domains are evolving from marketing assets into trust infrastructure underpinning cybersecurity, identity and interactions across the internet.
 As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
As power grids depend on microsecond precision, states must treat time synchronization as sovereign infrastructure, hardening satellite, fiber and orbital defenses against hybrid attacks that could trigger catastrophic blackouts through resilient sovereign time defense frameworks.
 ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
ICANN's court intervention in AFRINIC's winding-up case widens a local corporate dispute into a global Internet governance test, exposing weaknesses in RIR protections and strengthening calls for ICP-2 reforms to safeguard registry continuity.
 Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
Africa is rapidly emerging as a critical testing ground for AI governance, where fast adoption, evolving digital ecosystems, and uneven institutional readiness are exposing regulatory gaps with global implications.
 ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
ICANN's AFRINIC episode shows how support can harden into perceived authority. A standing RIR Boundary Protocol would force early warnings, role disclosure and procedural safeguards before regional engagement drifts into governance redesign.
 As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
As AI reshapes the digital world, online safety depends on balancing smarter protection with growing risks. From cybersecurity to privacy concerns, understanding AI's role can help users stay secure, informed, and resilient online.
 The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
The internet is fragmenting across cables, routing systems and governance. Most network engineers, focused on regional operations, are missing how technical infrastructure and state power are reshaping a once interoperable network.
 Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
Fake news spreads quickly online, fueling distrust, manipulation, and conflict. As AI-generated content grows more sophisticated, media literacy, fact-checking, and vigilance are essential to protecting online safety and preserving trust in information.
 Blank Domain Names Surpass Websites in Value for the First Time, Report Finds
Blank Domain Names Surpass Websites in Value for the First Time, Report Finds Iran Begins Restoring Internet After Record 88-Day Blackout
Iran Begins Restoring Internet After Record 88-Day Blackout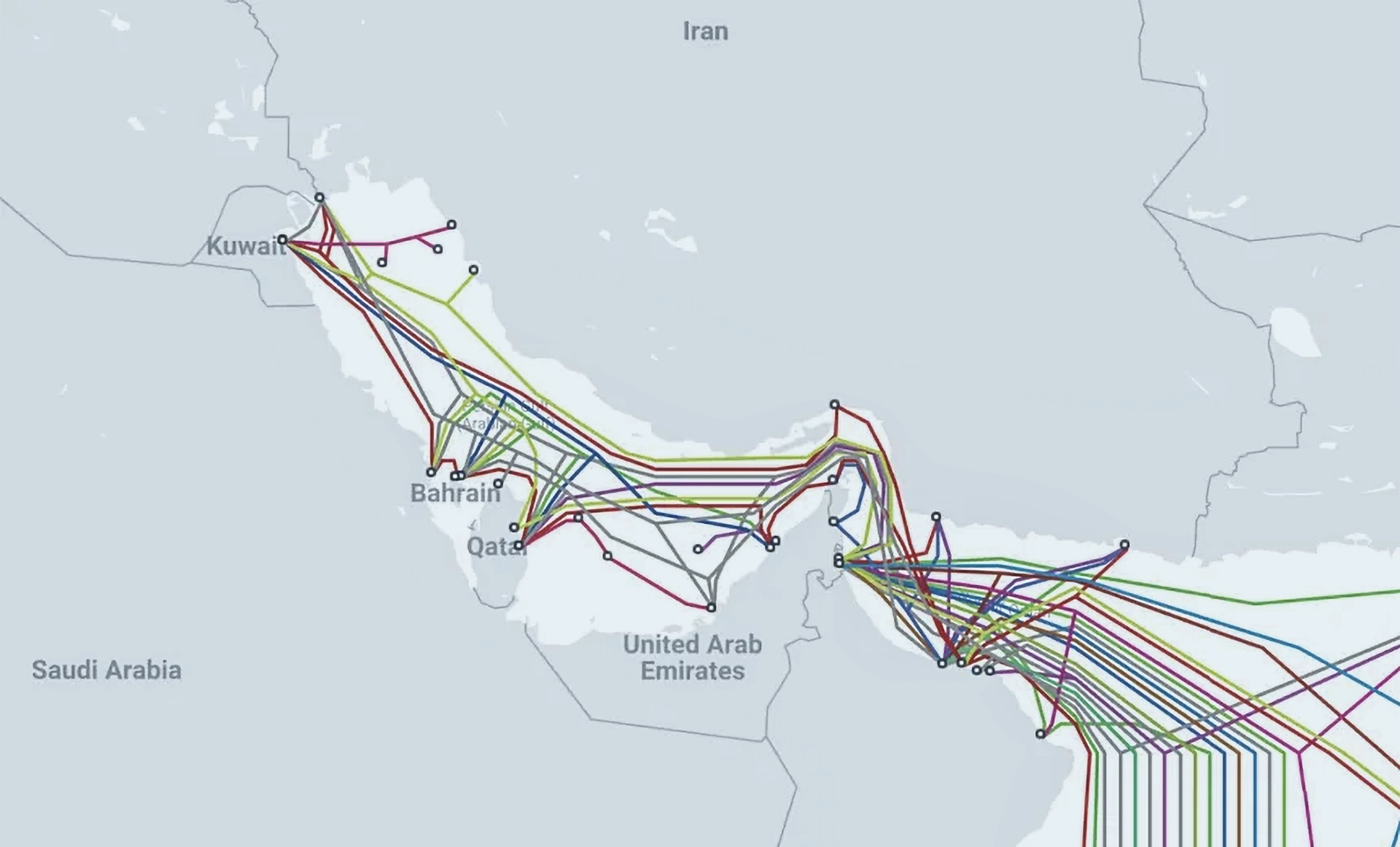 Iran Threatens Subsea Internet Cables in the Strait of Hormuz
Iran Threatens Subsea Internet Cables in the Strait of Hormuz Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity
Inside Iran’s Shift From Internet Shutdowns to Tiered Connectivity ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts
ICANN Opens New gTLD Applications for First Time Since 2012, With $227K Entry Fee and 27 Scripts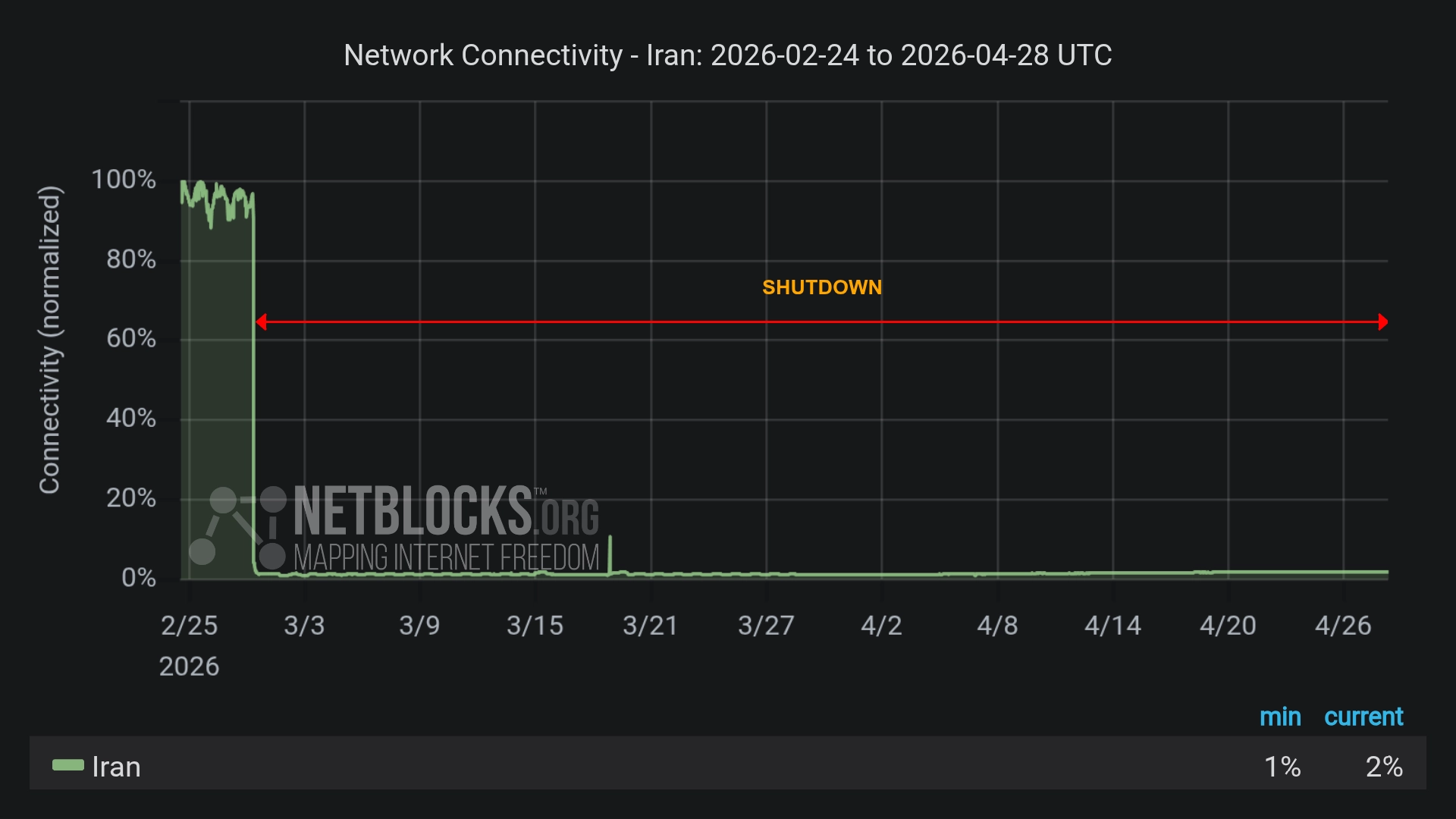 Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access
Iran’s Internet Blackout Hits 60 Days - Deepening Economic Crisis, Two-Tier Access U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears
U.S. Blocks Foreign-Made Routers Over Cybersecurity Fears Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks
Iran Targeted by Self-Propagating Malware in Supply-Chain Cyberattacks Iranians Outsmart Internet Blackout to Broadcast Airstrikes
Iranians Outsmart Internet Blackout to Broadcast Airstrikes