
 Americans who worried about governments somehow "running" the Internet through the United Nations failed to see the Trojan Horses that were rolled into ICANN's structure in 1998: the Governmental "Advisory" Committee and the special US Government powers over ICANN. The attempt by the US Commerce Department to "recall" the delegation of .xxx to ICM Registry due to pressure from deluded right-wing groups in the US who think that it will add to pornography on the Internet is a major inflection point in the history of ICANN, and could represent the beginning of the end of its private sector/civil society based model of governance. more
Americans who worried about governments somehow "running" the Internet through the United Nations failed to see the Trojan Horses that were rolled into ICANN's structure in 1998: the Governmental "Advisory" Committee and the special US Government powers over ICANN. The attempt by the US Commerce Department to "recall" the delegation of .xxx to ICM Registry due to pressure from deluded right-wing groups in the US who think that it will add to pornography on the Internet is a major inflection point in the history of ICANN, and could represent the beginning of the end of its private sector/civil society based model of governance. more
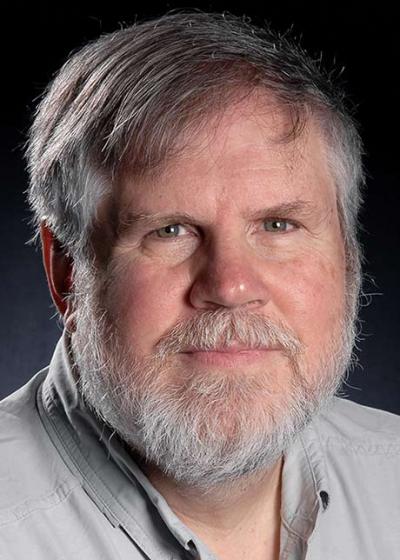
 Hi, I'm Richard. I've been around the Internet for a while. I work for Cisco now, and used to lead security for Firefox. I've published a few RFCs and served on the Internet Engineering Steering Group (the board of the IETF). I was a co-founder of Let's Encrypt and I currently serve on its board. I care about the Internet, and I care about nonprofits. more
Hi, I'm Richard. I've been around the Internet for a while. I work for Cisco now, and used to lead security for Firefox. I've published a few RFCs and served on the Internet Engineering Steering Group (the board of the IETF). I was a co-founder of Let's Encrypt and I currently serve on its board. I care about the Internet, and I care about nonprofits. more
It is sometimes said that: 'IP addresses are hoarded by "developed nations" - if only "underdeveloped" nations were given more IP addresses, the Internet would grow more/better...' Assertions like this mistakenly conflate the administrative process of requesting and receiving public IP addresses with the economic or commercial act of routing IP addresses - of engaging in what is sometimes called "Internet production." The former, administrative process involves relatively little in the way of overhead, and confers nothing more than the potential to develop public Internet resources -- i.e., to create new Internet users (provide access) and/or Internet uses (provide content and other online services). more
 On Thursday the 22nd, Robert Braver, an Oklahoma ISP owner who is a long time activist against both spam and junk faxes, received a default judgment of over $10 million against high profile spammer Robert Soloway and his company Newport Internet Marketing. Soloway has frequently been cited as one of the ten largest spammers in the world. more
On Thursday the 22nd, Robert Braver, an Oklahoma ISP owner who is a long time activist against both spam and junk faxes, received a default judgment of over $10 million against high profile spammer Robert Soloway and his company Newport Internet Marketing. Soloway has frequently been cited as one of the ten largest spammers in the world. more
As most readers are no doubt aware, when it comes to the topic of Top-Level Domains (TLDs), Internet Corporation for Assigned Names and Numbers (ICANN) takes center stage. Vint Cerf, Google's VP and Chief Internet Evangelist, who has served as chairman of the board of ICANN since the November of 1999 has accepted CircleID's invitation to directly respond to your questions on the topic. This is your opportunity to have your Top-Level Domain related questions responded by Vint Cerf. more
 Cloud computing has experienced exponential growth over the last few years. As of December 2013, almost 60 percent of current small-to-medium businesses (SMB) use cloud services, and 72 percent of these businesses virtualize substantial portions of their servers. The growth is only expected to increase over the next few years. Here are just a few of the major current trends in the industry today. more
Cloud computing has experienced exponential growth over the last few years. As of December 2013, almost 60 percent of current small-to-medium businesses (SMB) use cloud services, and 72 percent of these businesses virtualize substantial portions of their servers. The growth is only expected to increase over the next few years. Here are just a few of the major current trends in the industry today. more
 All those Internet Governance pundits who track ICANN the way paparazzi track Paris Hilton are barking up the wrong tree. They've mistaken the Department of Street Signs for the whole of the state. The real action involves words like rbldnsd, content filtering, and webs of trust. Welcome to the Internet! What's on the menu today? Spam, with some phish on the side! We've got email spam, Usenet spam, IRC spam, IM spam, Jabber spam, Web spam, blogs spam, and spam splogs. And next week we'll have some brand new VoIP spam for you. Now that we're a few years into the Cambrian explosion of messaging protocols, I'd like to present a few observations around a theme and offer some suggestions. more
All those Internet Governance pundits who track ICANN the way paparazzi track Paris Hilton are barking up the wrong tree. They've mistaken the Department of Street Signs for the whole of the state. The real action involves words like rbldnsd, content filtering, and webs of trust. Welcome to the Internet! What's on the menu today? Spam, with some phish on the side! We've got email spam, Usenet spam, IRC spam, IM spam, Jabber spam, Web spam, blogs spam, and spam splogs. And next week we'll have some brand new VoIP spam for you. Now that we're a few years into the Cambrian explosion of messaging protocols, I'd like to present a few observations around a theme and offer some suggestions. more
 Two events, which made headlines in the digital world in 2016, will probably frame the Internet Governance Agenda for 2017. October 1, 2016, the US government confirmed the IANA Stewardship transition to the global multistakeholder community. November 2, 2016, the Chinese government announced the adoption of a new cybersecurity law which will enter into force on July 1, 2017. more
Two events, which made headlines in the digital world in 2016, will probably frame the Internet Governance Agenda for 2017. October 1, 2016, the US government confirmed the IANA Stewardship transition to the global multistakeholder community. November 2, 2016, the Chinese government announced the adoption of a new cybersecurity law which will enter into force on July 1, 2017. more
CircleID recently interviewed Meng Weng Wong, the lead developer of Sender Policy Framework (SPF) and founder of Pobox.com. As one of the leading anti spam authentication schemes, SPF is used by companies such as AOL, Earthlink, SAP and supported by anti spam companies such as Sophos, Symantec, Brightmail, IronPort, Ciphertrust, MailArmory, MailFrontier, Roaring Penguin Software, and Communigate Pro. Last month, Microsoft announced its agreement to merge Caller ID, its own proposed anti spam authentication scheme, with SPF -- the joint standard is called 'Sender ID'. In this two-part interview, Meng Wong explains how SPF got started, where it is today and what could be expected in the future of email. more
 I feel incredibly lucky to work every day with some of the biggest, most recognised and most innovative organisations from around the world on developing strategies for their .brand TLDs. In this capacity, I also have the privilege to meet some of the most knowledgeable and forward-thinking experts in branding, digital marketing, web development and technology, to name a few. One such person is the brilliantly talented Matt Dorville. more
I feel incredibly lucky to work every day with some of the biggest, most recognised and most innovative organisations from around the world on developing strategies for their .brand TLDs. In this capacity, I also have the privilege to meet some of the most knowledgeable and forward-thinking experts in branding, digital marketing, web development and technology, to name a few. One such person is the brilliantly talented Matt Dorville. more
 The Internet is often a lawless place. Everyone knows that there are many tricks and traps lurking on the Internet, just waiting to prey on unsuspecting and innocent users. Some of these traps will trash your computer while others will turn your PC into a zombie that will broadcast messages at the virus writer's command. ...The list of annoyances and downright criminal activities seem endless. ...To make the Internet a safer place both legislators and law enforcement are now focusing on the Internet. In the crossfire that's taking place there are many ideas that are being offered up. Some of them are good and some are not. One bad decision that was recently forced upon the Internet community (without hearings -- more on this later) was to eliminate private domain name registrations for .US domain names. ...It's important to understand the difference between privacy and anonymity. more
The Internet is often a lawless place. Everyone knows that there are many tricks and traps lurking on the Internet, just waiting to prey on unsuspecting and innocent users. Some of these traps will trash your computer while others will turn your PC into a zombie that will broadcast messages at the virus writer's command. ...The list of annoyances and downright criminal activities seem endless. ...To make the Internet a safer place both legislators and law enforcement are now focusing on the Internet. In the crossfire that's taking place there are many ideas that are being offered up. Some of them are good and some are not. One bad decision that was recently forced upon the Internet community (without hearings -- more on this later) was to eliminate private domain name registrations for .US domain names. ...It's important to understand the difference between privacy and anonymity. more
 There are indications that the Internet, at least the Internet as we know it today, is dying. I am always amazed, and appalled, when I fire up a packet monitor and watch the continuous flow of useless junk that arrives at my demarcation routers' interfaces. That background traffic has increased to the point where it makes noticeable lines on my MRTG graphs. And I have little reason for optimism that this increase will cease. Quite the contrary, I find more reason to be pessimistic and believe that this background noise will become a Niagara-like roar that drowns the usability of the Internet. And the net has very long memory... more
There are indications that the Internet, at least the Internet as we know it today, is dying. I am always amazed, and appalled, when I fire up a packet monitor and watch the continuous flow of useless junk that arrives at my demarcation routers' interfaces. That background traffic has increased to the point where it makes noticeable lines on my MRTG graphs. And I have little reason for optimism that this increase will cease. Quite the contrary, I find more reason to be pessimistic and believe that this background noise will become a Niagara-like roar that drowns the usability of the Internet. And the net has very long memory... more
VoIP is here to stay. In fact many incumbent telecommunication carriers have started offering VoIP service for sometime and several new VoIP service providers have emerged. Aside from issues such as quality of service, the aspect of security, or lack thereof, is misunderstood by some of the VoIP service providers. This purpose of this article is to discuss two of the most well known attacks that can be carried out in current VoIP deployments. more
 For some years now the general uptake of IPv6 has appeared to be "just around the corner". Yet the Internet industry has so far failed to pick up and run with this message, and it continues to be strongly reluctant to make any substantial widespread commitment to deploy IPv6. Some carriers are now making some initial moves in terms of migrating their internet infrastructure over to a dual protocol network, but for many others it's a case of still watching and waiting for what they think is the optimum time to make a move. So when should we be deploying IPv6 services? At what point will the business case for IPv6 have a positive bottom line? It's a tough question to answer, and while advice of "sometime, probably sooner than later" is certainly not wrong, it's also entirely unhelpful as well! more
For some years now the general uptake of IPv6 has appeared to be "just around the corner". Yet the Internet industry has so far failed to pick up and run with this message, and it continues to be strongly reluctant to make any substantial widespread commitment to deploy IPv6. Some carriers are now making some initial moves in terms of migrating their internet infrastructure over to a dual protocol network, but for many others it's a case of still watching and waiting for what they think is the optimum time to make a move. So when should we be deploying IPv6 services? At what point will the business case for IPv6 have a positive bottom line? It's a tough question to answer, and while advice of "sometime, probably sooner than later" is certainly not wrong, it's also entirely unhelpful as well! more
In an RFC prepared by Donald E. Eastlake 3rd and Declan McCullagh, an analysis is offered for proposals to mandate the use of a special top level name or an IP address bit to flag "adult" or "unsafe" material or the like. This document explains why these ideas are ill considered from legal, philosophical, and technical points of view: "Besides technical impossibility, such a mandate would be an illegal forcing of speech in some jurisdictions, as well as cause severe linguistic problems for domain or other character string names." more
Sponsored byVerisign

Sponsored byDNIB.com

Sponsored byIPv4.Global

Sponsored byRadix

Sponsored byWhoisXML API

Sponsored byVerisign

Sponsored byCSC
